Biometrics in 2026 – Is Facial Recognition the Key to Ultimate Security or a Privacy Nightmare?
The discussion around security and privacy is reaching a fever pitch, and at its center is the rapid deployment of biometric technologies. Biometrics in 2026 represents a pivotal moment where facial recognition, fingerprint scans, and iris authentication are transitioning from niche security tools to pervasive elements of daily life. While proponents hail facial recognition as the ultimate key to swift, immutable identity verification and heightened security, critics warn that its widespread use heralds an unprecedented era of surveillance and privacy erosion. Understanding the dual nature of Biometrics in 2026 is essential for shaping its ethical future.
The Security Promise of Biometrics in 2026
The appeal of facial recognition in security is undeniable. Unlike passwords or physical keys, biometric data is unique, difficult to duplicate, and cannot be easily forgotten or shared. The advancements in Biometrics in 2026 promise several significant improvements:
The move toward Biometrics in 2026 offers a powerful layer of authentication that is inherently harder to spoof than traditional credentials.
The Privacy Nightmare Scenario
Despite the security benefits, the widespread adoption of facial recognition raises profound concerns about civil liberties and privacy. The primary fear surrounding Biometrics in 2026 is the creation of a surveillance society.
The challenge for policymakers dealing with Biometrics in 2026 is ensuring that security gains do not come at the cost of fundamental human rights.
The Regulatory and Ethical Landscape of Biometrics in 2026
The true direction of Biometrics in 2026 will be determined by regulation. Governments and industry bodies are grappling with the need for ethical guidelines, data localization requirements, and strict consent models. The development of privacy-preserving techniques, such as federated learning and on-device storage of biometric templates, offers a potential middle ground. These technologies aim to ensure that while the biometric match happens instantly for authentication, the raw, sensitive facial data never leaves the user’s device.
Ultimately, the successful integration of Biometrics in 2026 hinges on transparency and user control. If systems are built with privacy by design and clear accountability mechanisms, facial recognition can be a tool for security. If not, the nightmare scenario of ubiquitous, unconstrained surveillance will become a reality. Biometrics in 2026: Is facial recognition the key to unbeatable security, or a dystopian privacy nightmare? We explore the pros, cons, and future of surveillance tech.
You unlock your phone with a glance. You breeze through airport security without pulling out your passport. You enter your office building, and the door clicks open, recognizing you instantly. This isn’t science fiction; it’s the daily reality of biometric technology. And at the forefront of this revolution is facial recognition. As we look toward 2026, the technology is becoming exponentially more powerful, more integrated, and more common. Proponents hail it as the key to a safer, more seamless world—a world free from stolen keys, forgotten passwords, and anonymous threats.
But critics see a darker picture: a future of constant, unavoidable surveillance, where our most unique identifier—our face—is tracked, stored, and potentially misused. So, which is it? As a leader in the security space, we’re diving deep into the debate. Is facial recognition the ultimate security tool, or a privacy nightmare we’re sleepwalking into?
Facial Recognition as Ultimate Security
For security professionals, businesses, and homeowners, the benefits of advanced biometrics are undeniable. The “pro-security” argument rests on a few powerful pillars.
Unbeatable Access Control
Forget keycards that can be stolen, fobs that can be cloned, or PINs that can be shared. Your face is unique. By 2026, we expect to see high-resolution facial scanners as the standard for:
This technology doesn’t just identify who is allowed in; it instantly flags who isn’t, providing real-time alerts to security personnel.
A Powerful Tool for Public & Private Safety
In the public sphere, facial recognition is a game-changer for law enforcement. It can scan crowds to find a missing child or identify a person of interest in seconds. For private security firms, this scales down. Imagine a corporate campus, a shopping mall, or a large-scale event. An integrated system can:
Seamless and Frictionless Experience
Security often comes at the cost of convenience. We wait in lines, fumble for IDs, and memorize complex passwords. Facial recognition promises the opposite. It’s frictionless security. This seamlessness isn’t just a luxury; it improves security by reducing “tailgating” (people slipping in behind an authorized person) and ensuring that protocols are always followed.
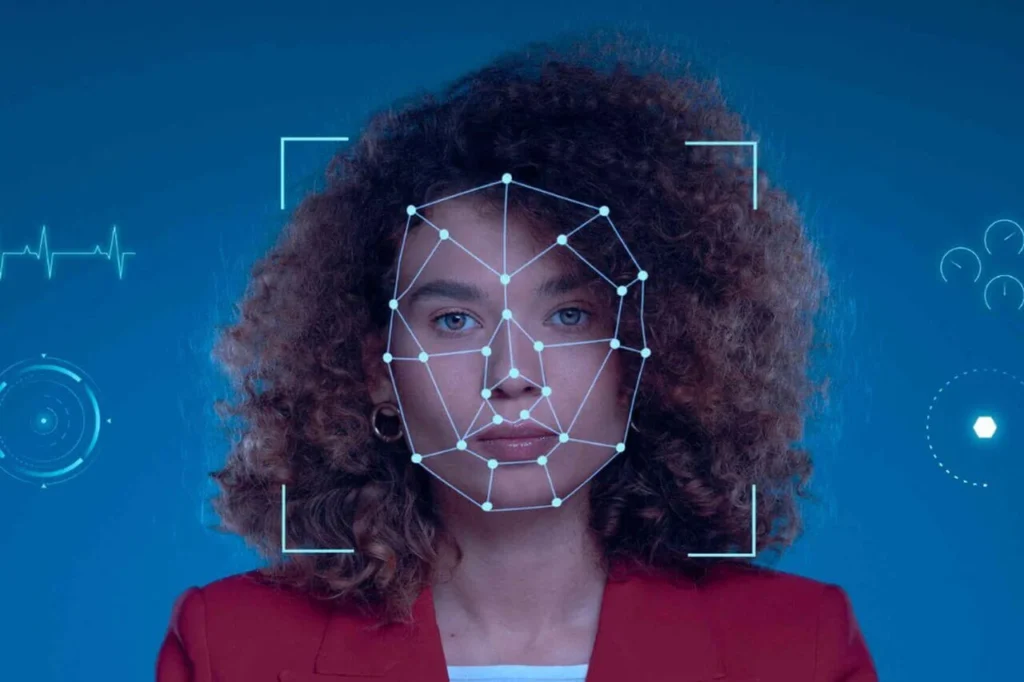
The Peril: A Privacy Nightmare in the Making?
This is where the debate gets heated, and for good reason. The same technology that provides “frictionless” security can also be used to create “frictionless” surveillance.
The Specter of Mass Surveillance

If a camera can identify a “person of interest,” it can also identify everyone else. Privacy advocates warn of a “Big Brother” scenario where governments or corporations could track citizens’ movements, associations, and presence at protests or private meetings. The question isn’t just “Can they do it?”—by 2026, the tech will be ubiquitous. The question is, “What stops them?”
“Who Has My Face?” The Data Breach Problem
Your password can be changed. Your credit card can be canceled. Your face is permanent.
What happens when a database storing millions of “faceprints” is hacked? This is a primary concern for 2026. Unlike other data, a stolen faceprint can be used to impersonate you, commit fraud, or track you indefinitely. The security of the data is just as important as the security the technology provides.
The Problem of Bias and Inaccuracy
Facial recognition algorithms are created by humans and trained on data sets. Historically, many of these systems have shown significant bias, performing less accurately for people of color, women, and transgender individuals.
A false negative (failing to identify an authorized person) is an inconvenience. A false positive (incorrectly identifying an innocent person as a criminal) is a life-altering disaster. While the technology is improving, the risk of algorithmic bias remains a critical ethical and legal hurdle.
Finding the Balance
So, where does this leave us? The year 2026 won’t be a simple choice between one or the other. Instead, it will be a battleground for finding a middle ground. We predict three key trends will define this balance:
A Tool, Not a Tyrant
At TheSecurePatrol.com, we believe that technology is ultimately just a tool. A hammer can be used to build a house or to break a window. The same is true for facial recognition.
By 2026, facial recognition will not be the key to ultimate security. It will be a powerful component of a comprehensive security strategy.
It will work alongside other measures—human patrol officers, smart monitoring, and strong data protection policies—to create a layered defense. The “nightmare” scenario is entirely avoidable, but it requires vigilance. It requires strong ethical guidelines, transparent policies, and robust data security. As a business or homeowner, the right question to ask your security provider isn’t just “Do you use facial recognition?” but “How do you protect the data you collect?”
What are Biometric Security Systems?
Biometric security systems provide advanced identity verification by analyzing unique physical and behavioral characteristics, such as fingerprints, facial features, iris patterns, and voice recognition. Unlike traditional methods like passwords or keycards—which are vulnerable to theft and duplication—biometric technology delivers a superior level of reliable and personalized protection that cannot be easily compromised.
What is Biometrics and How Does It Work?
Biometrics is the science of measuring and analyzing the physical or behavioral characteristics of individuals. Biometrics starts from the fact that humans have characteristics that are distinguishable from others. Such as fingerprints, facial features, iris patterns, tone of voice and hand geometry anatomical features it can be counted among. Signing style, walking style and keyboard usage behavioral characteristics it can be counted among.
Unlike traditional authentication methods, biometric measurements unforgettable, unlost and unpredictable he has qualities. Biometric technologies digitize these features a unique biometric template creates. The template creation process occurs by defining the distinguishing points of each biometric property and processing them through a mathematical algorithm.
For example, details such as bifurcating lines and endpoints can be decisive in fingerprints. In facial recognition, measurable features such as distance between the eyes, nose width and jaw structure are used. In addition to determining the uniqueness of the individual, biometrics also ensures the invariance and measurability of these data over time.
What are Biometric Security Systems?
Biometric security systems are technological solutions that authenticate people using their physical or behavioral characteristics. These systems provide access control by recognizing innate biological or behavioral characteristics specific to each individual. Biometric security systems data collection, processing, storage and comparison it consists of four basic components. Sensors and readers enable the collection of biometric data. Software components take the collected data, evaluate its quality and turn it into a template.
Created templates are stored in secure databases and used as reference points for authentication. The comparison engine decides on access by performing match analysis between live sampling and recorded templates. Biometric security systems are becoming smarter every day. More than one feature is now used together to improve security, rather than just a single biometric feature. For example, facial recognition and fingerprint reader the combination of systems provides much stronger security than systems based on a stand-alone feature.
| Traditional Security | Biometric Security |
| Passwords | Finger mark |
| PIN Codes | Face Recognition |
| Smart Cards | Iris Scanning |
| Keys | Voice Recognition |
| Identity Documents | Vein Recognition |
| The fullers | Hand geometry |
| It can be easily forgotten/lost | Unforgettable/Interlivable |
| Shareable/playable | Unshareable/hard to copy |
| Low security level | High level of security |
| Low cost | High initial cost |
How Do Biometric Security Systems Work?
Biometric security systems work by translating the physical characteristics unique to each person into digital patterns. Although it sounds complicated, it actually runs a systematic algorithm process in the background. In the first step, a recording process is carried out to make the system work. At this stage, biometric data such as fingerprints, face or iris are collected, quality checked and converted into a digital template. The created templates are stored in a secure environment to be used for later authentication. During the verification phase, when the user wants to access the system, he presents his biometric data again. The system receives this new data, processes it and compares it with the pre-recorded digital template. This comparison is made based on a certain similarity rate rather than a one-to-one match. Each system has a minimum threshold value that it agrees to recognize. If new data exceeds this threshold, the system recognizes the person and grants access.
To ensure accuracy in this process, two basic error metrics are taken into account: Incorrect Acceptance Rate (FAR) and Incorrect Rejection Rate (FRR). HEADLIGHT it indicates the possibility of accidental admission by a person who is not authorized to the system. FRR it refers to the risk of erroneous rejection by an authorized person. Advanced systems are constantly calibrated to operate at a balanced point between these two ratios. To take security one step further, biometric systems are often used as part of a multi-factor authentication structure. For example, some organizations require authentication not only with a fingerprint but also with a smart card.
Biometric Security System Types
Physical Biometric Systems
Physical biometric systems are built on the unique anatomical features of our body. These systems are based on innate physical characteristics that remain relatively unchanged throughout life.
Behavioral Biometric Systems
Behavioral biometric systems authenticate people by recognizing their characteristic behavioral patterns. These systems focus on behavioral traits that can change over time but are still distinctive.
Biometric Security Systems Usage Areas
Biometric security systems are used in a variety of industries thanks to their unique authentication capabilities. The safety and efficiency advantages provided by these technologies offer attractive solutions to organizations in different fields.
Advantages of Biometric Security Systems
Biometric security systems offer significant advantages over conventional authentication methods.
Things to Consider in Biometric Security Systems
In order for biometric security systems to operate effectively and safely, well-thought-out planning and a holistic approach are required. In order for systems to reach high security standards, some important points must be carefully evaluated.
Frequently Asked Questions
How Safely Is Biometric Data Stored?
Biometric data is generally stored in encrypted format and not in raw form. Modern systems create biometric templates that cannot be recycled to original biometric data. In some advanced systems, data can be stored on the user’s own device rather than a central database. By security standards, end-to-end encryption is used when transmitting data and database access is restricted by strict authorization policies.
How Are Failure Rates of Biometric Systems Evaluated?
Failure rates of biometric systems are measured by the FAR (False Acceptance Rate) and FRR (False Rejection Rate) metrics. FAR indicates the likelihood of an unauthorized person being mistakenly accepted by the system; Low FAR means higher security. FRR refers to the possibility of an authorized person being accidentally rejected by the system; Low FRR provides better user experience. The intersection between these two metrics is called “Equal Error Rate” (EER) and is used to evaluate the overall performance of the system. In modern biometric systems, the EER is usually below 1’%.
Securing Your Building: Biometric vs. Card Access Control
When it comes to securing modern buildings, choosing the right door access control system is crucial. Two popular options are card-based and biometric access control. Both offer distinct advantages and cater to different security needs. This article explores these door access systems in detail to help you decide which access control solution fits your building best.

What is a Door Access System?
A door access system is an electronic security solution that controls and monitors entry to buildings or restricted areas. Instead of relying on traditional keys, these systems use credentials such as smart cards, key fobs, or biometric data to grant authorized access.
How Door Access Control Systems Work
A door access control system operates by authenticating a user’s credentials, either a physical card or biometric trait, at a reader installed near the entry point. Once authenticated, the system signals the electronic lock to open. Every access attempt is recorded for audit purposes. These systems may support features such as remote unlocking, time-based restrictions, and integration with broader security monitoring. This approach offers businesses flexibility, fast entry processing, and robust security management for every door.
Exploring Biometric Door Access Control
Biometric door access control identifies individuals based on unique physical traits such as fingerprints or facial recognition.
Benefits of Biometric Door Access Systems
Challenges to Keep in Mind
Understanding Card Door Access Control
Card door access control systems use physical credentials like RFID cards, key fobs, or smart cards to grant entry. Users simply scan their card at an electronic reader to unlock doors.
Advantages of Card Door Access Control
Limitations of Door Access Systems to Consider
Biometric vs. Card Door Access Control
Choosing between biometric and card door access control systems depends on your building’s security needs and budget. Each system offers unique advantages to consider before making a decision.
| Feature | Biometric Access Control | Card Access Control |
|---|---|---|
| Security Level | Very high; unique physical traits | Good, with encryption and control |
| Cost | Higher upfront, lower ongoing costs | Lower upfront and maintenance |
| Ease of Use | Hands-free, uses unique biological traits | Requires carrying physical cards |
| Risk of Unauthorized Access | Nearly impossible to duplicate or share | Cards can be shared or lost |
| Administrative Overhead | Lower (no physical items to replace) | Moderate (card replacements, etc.) |
| Integration Capability | High, often combined with cards for 2FA | High (CCTV, alarms, payroll) |
| User Throughput Speed | Very fast (seconds) | Fast |
Which Door Access System is Right for Your Building?
Choosing the best door access control method depends on your building’s security requirements, budget, and user convenience priorities.
Making an Informed Decision
Whichever you choose, prioritizing advanced technology and trusted suppliers ensures a safer, smarter building environment.
Frequently Asked Questions
Unmasking Its Hidden Flaws and Risks
Facial recognition technology has made leaps and bounds, thanks to machine learning and artificial intelligence. These systems can now create lifelike images of human faces from scratch, using massive datasets of real images to learn and generate original content. However, recent incidents have exposed significant vulnerabilities in this technology.
Outsmarting the System
At the yearly Black Hat USA conference, McAfee researchers demonstrated how AI technology could be used to deceive facial recognition systems. By feeding a machine learning system 1,500 photos of two individuals, they created fake images that combined the facial features of both subjects. Over time, the system produced images that fooled the facial recognition system, misidentifying one individual as another.
Real-World Dangers
Steve Povolny, head of advanced threat research at McAfee, explained that this type of attack is not just theoretical. An attacker could submit a fake image of an accomplice for a passport application, which would then be stored in the passport database. If a live photo of the attacker is taken at an automated passport-verification kiosk, the system could identify the attacker as the accomplice, posing serious security risks.
McAfee’s Generative Adversarial Networks
The research involved the use of a Generative Adversarial Network (GAN) tool known as CycleGAN. GANs are AI neural networks that can create data similar to the input data. For instance, a GAN can generate fake but realistic images of human faces using a set of real images. CycleGAN, specifically, is used for image-to-image translation, focusing on significant features like eye placement and head shape.
The Risks of CycleGAN
Facial recognition technology is increasingly used by law enforcement agencies to identify suspects. McAfee’s research aimed to understand the potential implications and risks of this technology. The study underscored the need for better regulation and security measures to prevent misuse, as the technology could be exploited to frame innocent individuals or evade detection.
Protecting Your Privacy
Facial recognition technology raises significant privacy concerns. Companies like Clearview AI have developed applications that can analyze photos and provide extensive information about individuals. To safeguard your privacy, consider the following steps:
Securing Your Business
Businesses using facial recognition technology can take several steps to reduce the likelihood of attacks:
The Path Ahead
While facial recognition technology offers benefits in authentication and security, it is crucial to be aware of its vulnerabilities. Hackers and security researchers are continually finding ways to bypass these systems. By staying informed and advocating for better regulation, individuals and businesses can help mitigate the risks associated with facial recognition technology.
What is Facial Recognition System and How Does It Work?
Face recognition authentication systems are revolutionizing the landscape of modern security and operational efficiency. By leveraging fast, contactless, and reliable biometric data, facial recognition technology not only modernizes institutional access control but also significantly streamlines business workflows. This advanced technology stands out by offering a seamless balance between robust protection and user convenience.
What is Facial Recognition System?
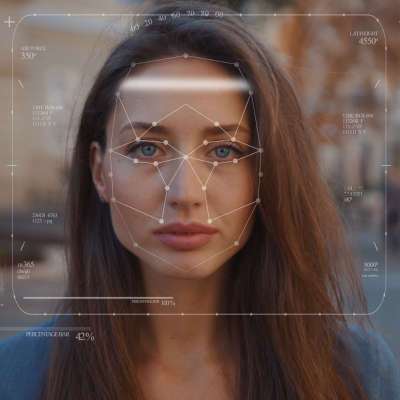
Facial recognition system identifies the person digitally by detecting and analyzing the characteristics of the human face. Facial recognition system is a biometric verification mechanism that continues its development today with artificial intelligence and deep learning algorithms. Facial recognition technology records more than 80’ unique points on each person’s face (such as distance between eye sockets, nose width, jawline structure, location of cheek bones) with digital mapping
The maps are converted into personalized mathematical formulas, creating a unique “face fingerprint”. The technology, which was initially developed for military and security purposes, is now used in many areas such as human resources management and the retail sector.
How Do Facial Recognition Systems Work?
Face Detection Phase
Facial recognition systems detect the presence of a human face from the image. Advanced algorithms, unlike other objects in the environment, determine the facial area by scanning the characteristic features of the human face such as oval shape, symmetrical structure, eye-nose-mouth positions. During the face detection phase, the system is optimized to recognize the face even from different angles, distances and light conditions.
Detection technology has evolved from traditional methods such as the Viola-Jones algorithm to deep learning systems based on today’s Evolved Neural Networks (CNN). Modern systems detect with an accuracy rate of up to 97’%, even when the face is partially visible, in low light conditions, or when accessories such as masks/glasses are used.
Feature Extraction and Analysis
After the face is detected, the system begins to remove the distinctive features of this face. Distances and angles between certain points on the face (eye corners, nose tip, lip edges, eyebrow line, chin line, etc.) are measured precisely.
Modern systems analyze 80-200 points and create a detailed face map. Feature extraction algorithms range from methods such as traditional Gabor wavelets and Local Binary Patterns (LBP) to deep learning models such as DeepFace and FaceNet. Deep learning (deep learning) models also learn the appearance of the face in different conditions and maintain the success of facial recognition despite variables such as aging, expression change, and beard/makeup condition.
Conversion to Digital Data
When facial analysis is performed, the information obtained is converted into a numerical data format. The created data format is called “face signature” or “face vector”. The face vector is generally a 128-256 dimensional vector. This mathematical representation functions as the digital counterpart of the physical face and becomes comparable and can be stored in the database.
The conversion process converts it into a sequence of code that reflects the physical properties of the face and does not directly contain the image of the face. In this way, it cannot be recycled to the original photo and data security is ensured. Very small amounts of data can be stored during this process. The face vector takes up approximately 4-8 KB of space.
Comparison and Matching
Finally, the resulting face vector is compared with the records in the database. For matching, a “similarity score is calculated. If the similarity score representing the mathematical distance between two face vectors is above a certain value, the system decides that there is a match.
In facial recognition systems, comparison is made between millions of records per second and the process is completed in milliseconds. Advanced systems make it easier to make decisions by generating a confidence score between possible matches.
Where is the Facial Recognition System Used?
Human Resources and Workplace Safety
Human resources departments use facial recognition systems in various operational processes. Facial recognition system may be preferred in security protocols to record the entry and exit of employees.
Personnel attendance tracking it replaces traditional card printing or fingerprint reading systems. Facial recognition-based attendance tracking systems can record employees’ entries and exits as they pass in front of the camera, without physical contact. Access control it ensures that only authorized personnel can enter sensitive areas within the company (server rooms, R&D laboratories, management floors).
It eliminates the risk of physical keys or access cards being lost, stolen or shared. The system keeps records of who is where and when and investigates possible security breaches. Workplace safety practices it is important in production areas where hazardous machines are located. The system minimizes the risks of work accidents by allowing only trained and authorized personnel to use certain equipment. Thanks to facial recognition technology, employees’ use of protective equipment (berets, glasses, masks) can also be controlled.
| Application Area | Traditional Method | Facial Recognition System | Productivity Increase |
| Personnel Attendance Tracking | Card printing / Signing | Automatic facial recognition | 34% time saving |
| Access control | Physical key/card | Contactless facial recognition | 78% faster entry |
| Educational Participation | Manual polling | Automatic facial recognition | 92% more accurate data |
| Overtime Tracking | Manual input | Automatic calculation | 45% error reduction |
| Security Breach Detection | Security personnel | Real-time alert | 62% faster intervention |
Facial Recognition in Daily Life
Facial recognition technology is also used in various areas of our daily lives. Facial recognition system is used in many areas such as unlocking mechanisms of smartphones and shopping experiences it improves user experienceA. Facial recognition on mobile devices It became very common in 2017’ with Apple’s Face ID technology. More than 65’% of smartphones use this technology. Users can unlock their mobile phones in seconds, avoiding the hassle of entering a password.
In the retail industry, facial recognition is often used to personalize the customer experience. Personalized discounts and suggestions can be offered by recognizing the previous shopping preferences of the customer entering the store. Safe-free store concepts such as Amazon Go can also automatically bill customers’ purchases with facial recognition technology.
Public Safety and Audit
One of the most common uses of facial recognition technology is public safety and control mechanisms. Facial recognition technology is used in important tasks such as law enforcement, border control and finding missing persons. Law enforcement actively uses facial recognition systems to identify suspects. Images obtained from camera recordings make it possible to identify suspects by comparing them with records in the police database.
Airports and border checkpoints widely use facial recognition systems in passenger authentication. This technology speeds up passport controls and prevents the use of fake IDs. The “Smart Gates” system implemented at Dubai Airport reduced passenger processing time to an average of 7-9 seconds. Facial recognition technology plays a life-saving role in finding missing persons, especially for children and the elderly. By uploading the photo of the missing person to the system, matching images obtained from city cameras can be made.
Advantages of Facial Recognition Technology
Facial recognition technology offers several advantages:
Facial Recognition and Data Security – KVKK and GDPR Compliance
Facial recognition technology is of particular importance for the protection of personal data. Biometric data is classified as “special personal data” within the scope of the Personal Data Protection Law (KVKK) in Turkey and the General Data Protection Regulation (GDPR) of the European Union. Considering KVKK explicit consent is mandatory for the use of facial recognition systems. Human resources departments must obtain an informed consent form from employees regarding the use of this technology.
In addition, companies using these systems must clearly state the purpose of processing the data, storage period and security measures. Biometric data only according to Article 6 of the KVKK with the express consent of the data subject or it can be processed in cases stipulated by law.
From a GDPR perspective facial recognition data Under Article 9 Personal data with “special categories is considered as ”. Strict conditions have been introduced for the processing of facial recognition data:
Recommended data security approaches for human resources:
Things to Consider When Choosing a Facial Recognition System for Human Resources
There are some points to consider when choosing the right facial recognition system for human resources departments.
Factors to consider when choosing a system are:
Cost analysis should include the total cost of ownership (TCO), not just the initial investment.
In this context:
Free time ideal for use in human resources and workplace safety facial recognition system devices it offers. ZKTeco and Soyal models quick recognition, multiple biometric support (fingerprint, card access system RFID card reader it can increase operational efficiency with its ‘s) and high security features.
Frequently Asked Questions
Is the Facial Recognition System Affected by Changes Such as Glasses, Beards or Makeup?
Modern facial recognition systems are minimally affected by changes such as glasses, beard and light make-up. Advanced algorithms can perform accurate recognition by focusing on the unchanging basic features of the face. However, accessories that prevent complete recognition may reduce the accuracy of the system.
How to Get Permission from Employees to Use a Facial Recognition System?
Before applying a facial recognition system, employees should be given clear and understandable information. The information provided should include the purpose for which the data will be used, how it will be protected, how long it will be stored and the rights of employees. Within the scope of KVKK, “Open Consent Text should be prepared and written approval should be obtained from employees. Employees’ choice rights can be protected by offering alternative authentication methods.
Can Facial Recognition System Be Used in Overtime Tracking and Overtime Calculations?
Facial recognition-based follow-up systems increase the accuracy of working hours by automatically and error-free recording of employees’ entry and exit times. It also creates a reliable data set that can be referenced in overtime calculations. This data can be integrated with payroll systems.