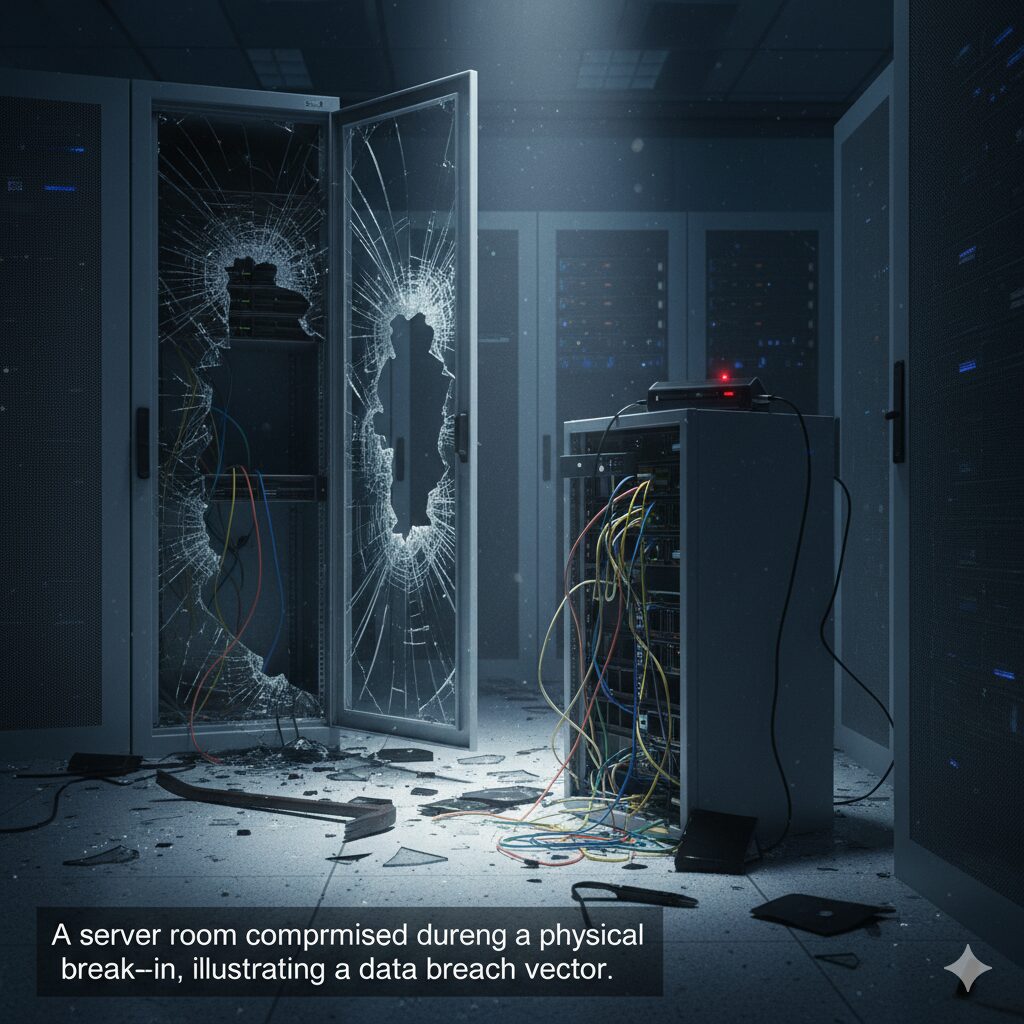
Post-Breach Forensics – What Happens When a Physical Break-In Becomes a Data Breach?
The intersection of physical intrusion and digital theft presents one of the most complex challenges in modern security. Post-Breach Forensics in these blended incidents requires specialized expertise to reconstruct the timeline and scope of the damage. When a seemingly isolated physical break-in—such as stolen hardware or unauthorized access to a server room—results in a significant data exposure, the subsequent Post-Breach Forensics investigation must meticulously bridge the gap between tangible evidence and digital logs. Understanding this integrated process is essential for legal compliance, remediation, and preventing future convergence attacks.
The Convergence Incident – A New Challenge for Post-Breach Forensics
The traditional separation between physical security teams and IT security teams dissolves the moment an intruder uses a physical presence to gain digital access. This scenario complicates Post-Breach Forensics significantly because the typical cyber tools may not capture the initial point of entry.
Why Physical Access Escalates Digital Risk
Phase 1 – Securing the Scene and Collecting Physical Evidence
The initial steps in Post-Breach Forensics must adhere to the chain of custody rules applicable to both criminal (physical) and digital investigations.
1. Physical Documentation
2. Digital Triage on Compromised Hardware
Phase 2 – Integrated Digital Forensics and Timeline Reconstruction
This phase involves correlating the physical evidence with the digital activity logs. The success of Post-Breach Forensics hinges on linking the physical intrusion timeline to the system activity timeline.
1. Log Correlation and Anomaly Detection
2. Identifying the Data Compromised
The core goal of Post-Breach Forensics is determining what data was accessed, modified, or exfiltrated.
Reporting and Remediation
The final output of Post-Breach Forensics dictates regulatory reporting, liability, and future security investment. The detailed report must clearly state how the physical intrusion facilitated the digital breach, which data was affected, and the attacker’s method of operation (TTPs). By rigorously applying integrated Post-Breach Forensics, organizations not only satisfy legal obligations but also gain the necessary intelligence to close the physical-digital security gaps permanently.
Imagine this: You walk into the office on a Monday morning. A window is smashed, a doorjamb is splintered. It’s a classic physical break-in. But the petty cash is still there, and the high-end laptops seem untouched. The real target? Your server room. In today’s hyper-connected world, a physical breach is often just the opening act for the main event: a catastrophic data breach. But what happens next? This is where post-breach forensics begins—the critical investigation that uncovers what really happened.
From Broken Lock to Stolen Data
We often think of security in two separate buckets: the security guard at the front desk (physical) and the firewall protecting the network (digital). Attackers don’t see that line. To them, a building is just a physical firewall to bypass. A physical break-in is a high-risk, high-reward move. The attacker is betting that once they are inside, your digital defenses are weak.
How it typically unfolds:
By the time your physical security team discovers the broken window, the attacker is gone—and your company’s most sensitive data is going with them.
Inside the Post-Breach Forensics Process
When a physical break-in is suspected to be a data breach, a specialized “forensics” team is activated. This isn’t just your IT guy; it’s a team of investigators (internal or external) trained to preserve and analyze evidence. Their goal is to answer critical questions—and fast.
Phase 1: Securing the “Crime Scene” (Physical & Digital)
Before a single file is analyzed, the scene must be preserved.
Phase 2 – The Forensic Investigation Play-by-Play
Once the scene is secure, the real deep-dive begins. Investigators are looking for the “digital fingerprints” that connect the physical entry to the digital theft.
1. Creating a Forensic Image: Investigators don’t work on the original hard drive. They create a “forensic image”—a perfect, bit-for-bit copy. This preserves the original evidence (maintaining the “chain of custody,” which is vital for legal action) and allows them to safely perform analysis on the copy.
2. Analyzing the Physical Evidence: The team correlates physical data with digital questions:
3. Correlating the Digital Evidence: Now, they look at the digital logs within that exact 10-minute window.
Here’s an illustration of how physical and digital evidence come together:

The Aftermath – Why This Matters for Your Business
The forensic report isn’t just an “IT problem”—it’s a “CEO problem.” The findings determine the next, often painful, steps.
Prevention – Hardening the “Phygital” Perimeter
A post-breach investigation will always reveal one thing: prevention is infinitely cheaper than recovery. Here’s how you merge your physical and digital defenses.
Your Security is Only as Strong as Its Weakest Link
A physical break-in that becomes a data breach is a nightmare scenario because it proves that your security strategy had a critical blind spot. The wall between “physical security” and “cybersecurity” no longer exists. Post-breach forensics is the complex, high-stakes process of rebuilding the story of the attack. But your goal should be to never need it. By investing in an integrated security posture that treats your doors with the same seriousness as your firewalls, you can ensure your data—and your business—are secure from every angle.