The 2026 CISO’s Dilemma – Why Your Cybersecurity Budget is Wasted Without Physical Security
In the rapidly evolving threat landscape of 2026, the Cybersecurity Budget is no longer a necessary expense; it is a strategic investment directly enabling business resilience, competitive advantage, and customer trust. Chief Information Security Officers (CISOs) must navigate increasing threats—from sophisticated AI-driven attacks to persistent supply chain vulnerabilities—while facing pressure to demonstrate tangible Return on Investment (ROI) from the Cybersecurity Budget.
The key to a successful 2026 Cybersecurity Budget lies in strategic allocation, risk-based prioritization, and a shift from managing tools to managing exposure and outcomes. Every line item in the Cybersecurity Budget must be justified by its ability to mitigate a quantifiable business risk.
Anchoring the Cybersecurity Budget to Business Risk and Objectives
A common pitfall is allocating funds based on legacy spending or vendor promises. A modern, SEO-friendly Cybersecurity Budget starts with a clear understanding of the organization’s most valuable assets and critical risks.
- Risk-Based Prioritization: Conduct a comprehensive risk assessment. Security spending should correlate directly with the potential financial and reputational impact of a breach. Prioritize protecting the “crown jewels” over low-impact assets. This ensures every dollar in the Cybersecurity Budget delivers maximum protective value.
- Align with Business Goals: Present the Cybersecurity Budget not as a list of tools, but as a roadmap supporting key business initiatives. For example, if the goal is global expansion, the Cybersecurity Budget must fund advanced Cloud Security and Compliance frameworks.
- The Cost of Inaction: Clearly articulate the true cost of inaction to justify the size of the Cybersecurity Budget. Proactive security investment funded by the Cybersecurity Budget is significantly cheaper than breach recovery.
Key Investment Categories for the 2026 Cybersecurity Budget
While technology dominates spending, a resilient Cybersecurity Budget maintains a balance across three critical pillars: People, Process, and Technology.
A. Technology Tools & Platforms
The trend is shifting from point solutions to consolidated security platforms to optimize the Cybersecurity Budget.
- Zero Trust Architecture (ZTA): Moving away from perimeter-focused defenses. A significant portion of the Cybersecurity Budget should be allocated to Identity and Access Management (IAM), Microsegmentation, and strong Multi-Factor Authentication (MFA).
- Cloud Security: As cloud adoption grows, the Cybersecurity Budget must prioritize tools for Cloud Security Posture Management (CSPM) and Data Security Posture Management (DSPM) to maintain visibility and control.
- Continuous Exposure Management (CTEM): Allocate funds from the Cybersecurity Budget for continuous validation programs, like Penetration Testing as a Service (PTaaS), to get an always-on view of the attack surface.
B. People and Skills Investment
Technology is only as effective as the team managing it, making this a crucial component of the Cybersecurity Budget.
- Talent Retention and Development: Dedicate a significant portion of the Cybersecurity Budget to competitive compensation, professional development, and certifications.
- Security Awareness Training: Invest in frequent, engaging, and simulated phishing/incident training programs. This area provides one of the highest ROIs within the entire Cybersecurity Budget.
C. Process, Compliance, and Response
These non-technology items are crucial for operational maturity and must be funded within the Cybersecurity Budget.
- Incident Response (IR) Planning: Fund regular IR simulation and tabletop exercises from the Cybersecurity Budget to ensure the team is prepared.
- Regulatory Compliance: Allocate part of the Cybersecurity Budget for specialized data privacy audits and implementing controls required by evolving global regulations.
Optimizing and Measuring the Cybersecurity Budget for ROI
Maximizing the value of every dollar in the Cybersecurity Budget is achieved through strategic cost management and transparent metric reporting.
- Consolidate and Eliminate Tool Sprawl: Audit your current stack. If multiple tools have overlapping capabilities, consolidate to a single, integrated platform. This significantly reduces licensing costs and complexity within the Cybersecurity Budget.
- Focus on Metrics that Matter: Report key performance indicators (KPIs) to the board to justify the Cybersecurity Budget:
- MTTR (Mean Time to Respond/Remediate): The speed at which security issues are fixed.
- Risk Reduction Score: A measurable indicator of how new investments, funded by the Cybersecurity Budget, have lowered the overall risk profile.
By making the Cybersecurity Budget agile, measurable, and intrinsically tied to the organization’s risk profile, CISOs can transform their spending from a drain on resources into the very engine that drives sustainable, secure growth.
Cybersecurity Budget is very important. In the complex threat landscape of 2026, the Chief Information Security Officer (CISO) faces a critical dilemma: the growing disconnect between vast cybersecurity spending and the lingering, often overlooked vulnerabilities in physical security. Throwing millions at next-generation firewalls, AI-driven threat detection, and Zero Trust architectures is financially sound, yet a single, unbadged entry, a dropped USB drive, or an unsecured server room can render all that digital investment completely moot.
The reality is that attackers are not limited to the digital realm. They leverage the easiest point of entry, which is increasingly the convergence point between the physical and digital worlds. For modern CISOs, a budget that solely prioritizes virtual defenses is a budget half-spent, leaving the organization dangerously exposed to tangible, high-impact threats.
The Physical Door is the Digital Backdoor
The concept that a robust digital defense can withstand a compromised physical perimeter is a dangerous relic of the past. The year 2026 sees the convergence of physical and digital security as not just a trend, but a fundamental requirement for organizational resilience.
The Blurring Lines: Attack Vector Convergence
Attackers are masters of exploiting the weakest link. In a converged threat model, a physical breach often directly facilitates a catastrophic cyber event, and vice-versa:
- Physical to Digital: An attacker gains unauthorized access to a building (due to tailgating or a lapse in access control) and plugs a malicious device into an internal network port, or simply steals a device containing sensitive data. This completely bypasses the most sophisticated perimeter security.
- Digital to Physical: A hacker exploits an IoT vulnerability (e.g., an unpatched IP camera or HVAC system) to gain a foothold on the internal network. From there, they could disable physical access controls, sabotage operational technology (OT) systems, or trigger fire alarms to create a distraction for a secondary physical intrusion.
As one industry expert noted, attackers are “utilizing digital access to gain physical access, or they’re using physical access to gain digital access.” Ignoring one side of this equation creates a critical resilience gap.

The Hidden Costs of Neglecting the Physical Perimeter
When a security incident occurs, the financial impact extends far beyond the immediate cost of remediation. For a CISO to justify a balanced, converged budget, they must quantify the waste associated with an incomplete security posture.
Wasted Cybersecurity Investment
Every dollar spent on a Security Operations Center (SOC), threat intelligence platform, or Managed Detection and Response (MDR) service is undermined if the physical controls are weak. Why invest in multi-factor authentication for remote access when a criminal can simply walk into an office, steal a laptop, and get the credentials that way? This is the definition of a wasted budget—premium digital locks on a wide-open physical door.
Regulatory and Reputational Damage
In 2026, regulatory bodies like the EU, along with industry-specific compliance standards, are increasingly demanding holistic security controls. A breach stemming from a physical lapse (like improperly disposed media containing customer data, or an unmonitored server room) still incurs the same hefty fines and regulatory penalties as a purely digital attack. Furthermore, a highly visible, physically-enabled breach can cause irreparable reputation damage and a significant loss of customer trust.
Building a Converged Security Strategy for 2026
The CISO’s role must evolve from just securing IT systems to becoming the Chief Resilience Architect for the entire organization. This requires breaking down departmental silos and integrating technology and policy.
1. Converge Identity and Access Management (IAM)
This is the most crucial step. Physical access control (e.g., key cards, biometrics) should be integrated with digital IAM systems (e.g., Active Directory, Okta).
- Unified Auditing: If an employee’s digital access is revoked, their physical access should be automatically terminated simultaneously.
- Contextual Access: Use physical location data (e.g., “User logged in from the server room”) to inform and strengthen digital authentication requirements.
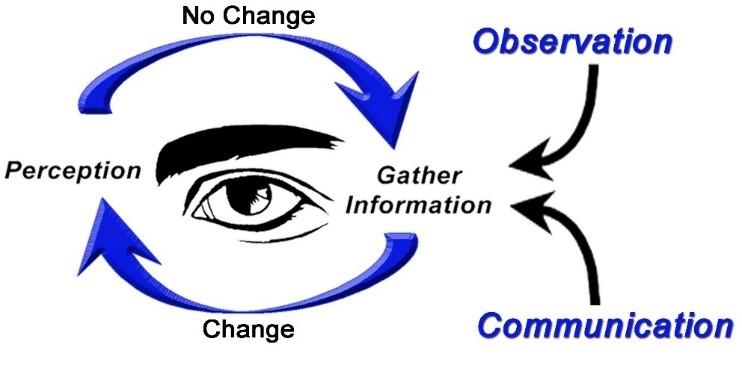
2. Integrate Physical and Digital Monitoring
Treat alerts from physical security systems (door ajar sensors, security cameras, environmental controls) as security events that feed directly into the SIEM (Security Information and Event Management) platform alongside digital logs.
- Scenario-Based Alerts: A door-forced-open alert that occurs simultaneously with a high volume of file transfers from a nearby workstation is a critical, converged incident demanding immediate response.
- IoT/OT Security: Actively monitor all Internet of Things (IoT) and Operational Technology (OT) devices (e.g., smart lights, building automation) as they represent a physical entry point for digital attack.
3. Prioritize Training and Physical Data Hygiene
The human factor is still the weakest link, both in cyber and physical security.
- Anti-Tailgating Awareness: Regular training is essential to reinforce policies against “tailgating” and the importance of challenging unrecognized individuals.
- Secure Disposal: Enforce strict policies for the secure destruction of all sensitive papers, hard drives, and USB media before disposal, preventing “dumpster diving” for corporate secrets.
The Call to Action for CISOs
In 2026, the dilemma is clear: a siloed security budget is a vulnerable budget. Cybersecurity resilience cannot be achieved with digital tools alone. CISOs must champion the convergence of physical and digital security to maximize the ROI of their overall security spending. By viewing the entire enterprise—from the front door to the cloud—as a single, interconnected attack surface, organizations can finally move past “checkbox security” and achieve true, enduring resilience.
Are you pouring millions into digital defense while leaving the front door unlocked? Discover the critical link between physical security and cyber defense that CISOs in 2026 can’t ignore.
The Hard Truth About Your 2026 Security Budget
Let’s be blunt. As a CISO, your primary battleground is digital. You’re fighting sophisticated phishing campaigns, zero-day exploits, and persistent nation-state actors. Your budget reflects this, with millions allocated to endpoint detection, cloud security, and AI-driven threat intelligence.
But here’s the dilemma that will define 2026: What good is a $10 million firewall if a $10-an-hour contractor can walk into your server room and plug in a USB?
We’re approaching a critical inflection point where the digital and physical worlds have completely converged. Yet, many organizations still treat cybersecurity and physical security as separate, siloed functions. This isn’t just an oversight; it’s a catastrophic vulnerability that’s actively wasting your cybersecurity budget.
Here’s why your digital fortress is set to crumble without a physical foundation.
The “Air Gap” Is a Myth – Today’s Top 5 Physical Breaches That Kill Cyber Budgets
That “air-gapped” network or secure data center isn’t as isolated as you think. Every digital defense has a physical key. Your budget is being wasted not because your cyber tools are failing, but because your physical protocols are giving attackers an easy pass.
1. The Tailgate & The “Friendly” Stranger
It’s the oldest trick in the book, and it works. An attacker, often disguised as a delivery driver or a fellow employee, simply follows an authorized person into a restricted area.
- How it Wastes Your Budget: That multi-million dollar Intrusion Detection System (IDS) is useless when the attacker is already inside the network, plugging directly into a conference room port. They bypass the entire digital perimeter.
2. The Unsecured Server Room & The Insider Threat
Whether it’s a disgruntled employee or a “trusted” third-party vendor, an attacker with legitimate physical access is your worst nightmare.
- How it Wastes Your Budget: Your expensive Data Loss Prevention (DLP) software is designed to stop large data exfiltrations over the network. It can’t stop someone from walking out the door with a hard drive or a laptop containing your entire customer database.
3. The “Find-Me” Attack: Discarded & Unattended Devices
A corporate laptop left in a rideshare. A company smartphone swiped from a coffee shop. An old hard drive improperly discarded in a dumpster.
- How it Wastes Your Budget: All the encryption and endpoint security you paid for relies on a user not handing the physical device over to an attacker. Once they have the hardware, it’s a matter of time before they bypass local security, access cached credentials, and pivot into your cloud environment.
4. The Exposed IoT & Critical Infrastructure
From smart thermostats and security cameras to industrial control systems (ICS), your network is connected to the physical world. These devices are notoriously insecure.
- How it Wastes Your Budget: An attacker can manipulate a building’s HVAC to overheat a data center, causing a physical shutdown that your cyber-attack simulations never accounted for. Your uptime budget is gone, not from a DDoS, but from a “phygital” attack.
5. The Siloed Response: When Your Teams Don’t Talk
A security guard spots a suspicious person near the data center, but they have no way to instantly alert the Security Operations Center (SOC). The SOC detects a strange login from inside the building, but they assume it’s a trusted user.
- How it Wastes Your Budget: You are paying for two separate, expensive security teams that are blind to each other’s data. This lack of integration creates massive response delays, allowing a small incident to escalate into a full-blown, budget-destroying breach.
Shifting from Silos to “Converged Security”
The only solution to this dilemma is Converged Security—a holistic strategy where physical security, cybersecurity, and personnel security are managed under one integrated framework. In this model, data from your access control systems (who entered which door and when) is fed directly into your SIEM (Security Information and Event Management) platform.
Think about this: Your system flags an impossible scenario—an employee’s badge is used to enter the New York office while their user account is simultaneously logging in from a laptop in Tokyo. A siloed system sees two “valid” events. A converged system sees a critical, undeniable breach in progress.
Stop Wasting Your Budget Today
Protecting your 2026 budget starts now. Don’t wait for a physical breach to expose your digital gaps.
- Conduct a “Phygital” Risk Assessment: Stop auditing your cyber and physical security separately. Hire experts to perform a converged audit. Ask them: “How could you physically get to our most critical data?”
- Unify Your Teams: Get your CISO and your Director of Physical Security in the same room, reporting to the same executive. Mandate shared intelligence and integrated response drills.
- Invest in Integrated Tech: Look for platforms that blend physical access control with digital identity management. Your employee’s digital identity should be their single key for everything, from logging into their laptop to entering the building.
Your Firewall Can’t Stop a Crowbar
As a CISO in 2026, you will no longer be judged just by your ability to stop malware. You will be judged by your ability to secure the entire organization, from the cloud to the concrete. Your cybersecurity budget is a powerful tool, but it’s only half the equation. By ignoring the physical perimeter, you aren’t just leaving a door unlocked—you’re actively setting your investment on fire.