Boosting Employee Awareness: The Power of Phishing Tests
Understanding Phishing Attacks Phishing attacks are a pervasive threat that every internet user should be aware of. In simple…
Cyber Security

Understanding Phishing Attacks Phishing attacks are a pervasive threat that every internet user should be aware of. In simple…

Understanding OWASP and Its Importance The Open Web Application Security Project, commonly known as OWASP, is a pivotal resource…

Why MSPs Must Prioritize Regular Risk Assessments In today’s rapidly evolving digital landscape, cybersecurity threats are becoming more sophisticated…

Understanding Contact Tracing During the COVID-19 pandemic, contact tracing has become an essential tool in slowing the virus’s spread….

Garmin’s Ransomware Attack: A Comprehensive Overview If you’re an avid runner or cyclist, you’ve likely heard about the recent…
Facial recognition technology has made leaps and bounds, thanks to machine learning and artificial intelligence. These systems can now…

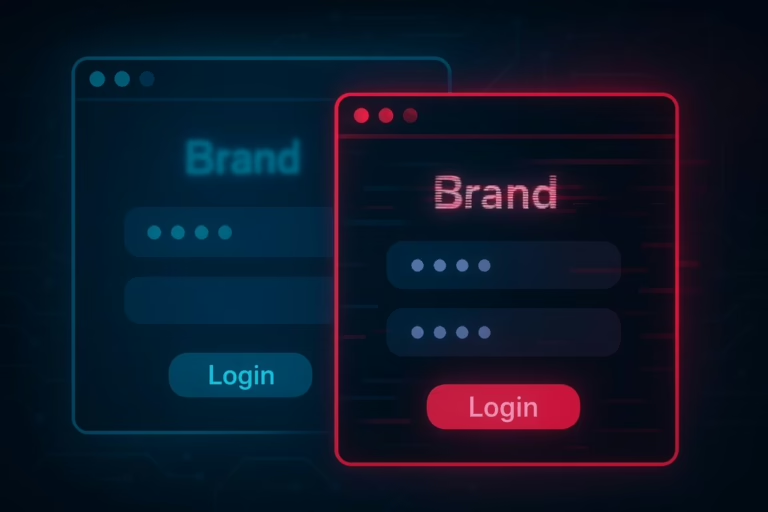
In today’s interconnected world, cyber threats are evolving rapidly. One such threat, which we’ve termed the “Domino Attack,” can…
In the realm of cybersecurity, threats don’t always come from sophisticated malware or zero-day exploits. Sometimes, they stem from…

Welcome to Cyber Hoot Wednesday Grab a cup of coffee, sit back, relax, and read on! We’re glad you’re…
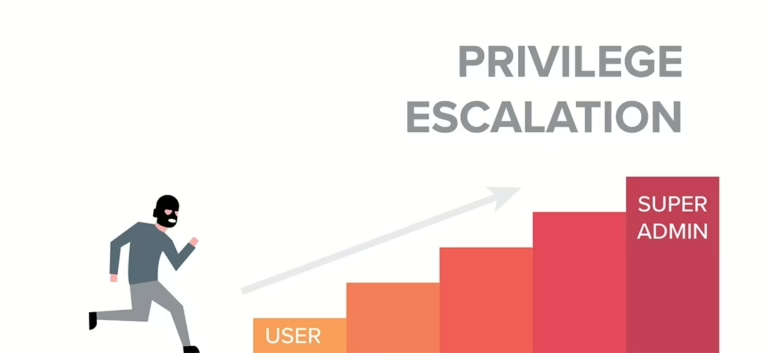
During penetration testing, after gaining access to a machine, different stages are required. If the infiltration is performed through…
End of content
End of content