Upgrade Your Tech: Unleash Enhanced Security & Peak Efficiency
Why Upgrading Your Tech is Essential for Security and Efficiency Just like the ancient pyramids of Egypt and the…
Cyber Security

Why Upgrading Your Tech is Essential for Security and Efficiency Just like the ancient pyramids of Egypt and the…

Remember the QR code craze of 2020? We scanned them for restaurant menus, parking meters, and even wedding guestbooks….

The Alarming Rise of AI-Powered Phishing Kits: A Growing Cyber Threat Gone are the days when phishing emails were…
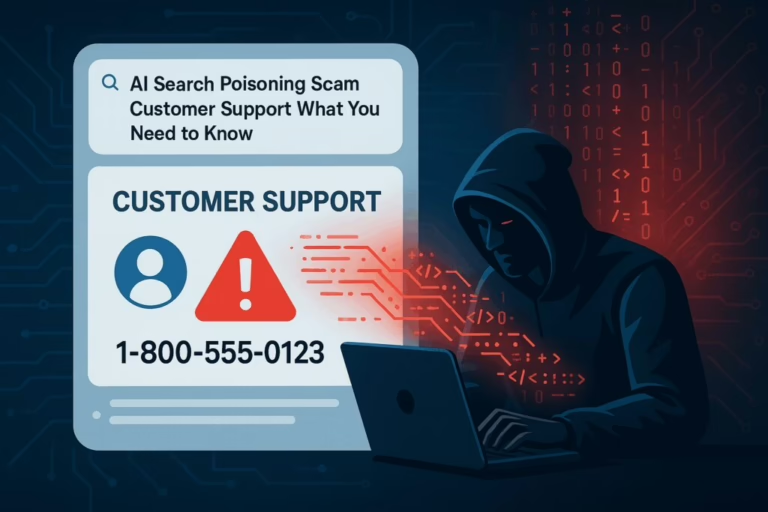
AI Poisoning: How Fake Support Scams Are Infiltrating AI Search Tools As internet users shift their attention, cybercriminals are…

Introduction to iSMET In the realm of penetration testing, we often find ourselves in need of specialized tools. Among…

Boosting Cybersecurity: The Impact of Automated Vulnerability Scanning and Penetration Testing In our fast-paced digital world, automated vulnerability scanning…

The Importance of Operating System Patches Operating system vendors continuously identify and fix flaws in their code, releasing updates…

Strengthening Your Team: The Ultimate Guide to Building a Human Firewall As work environments evolve, cybercriminals find new opportunities…

MongoBleed: A New Security Nightmare Remember Heartbleed? That security scare from a few years ago that had everyone changing…

Red Team Solutions: Enhancing Cybersecurity with Proactive Measures We are living in an era of rapidly advancing technology. As…
End of content
End of content