Boosting Security with Advanced Keyless Entry Systems – Access control systems
Access control systems are a cornerstone of contemporary security setups, offering keyless entry to protected zones like buildings, rooms, or facilities. These systems employ a variety of technologies to oversee and regulate access, delivering heightened security and convenience.
Understanding Access Control Systems
Access control systems are security measures that dictate who can enter or leave a designated area. They utilize a blend of hardware and software to verify users and permit or refuse access based on established criteria. These systems do away with traditional keys, opting instead for electronic credentials like smart cards, smartphones, PIN codes, or biometric data that can recognize fingerprint, vein, face, and iris patterns.
With our’s Access Control Systems, you can be confident that your premises are well-protected. Don’t delay until it’s too late. Assume command of your security now.
Advantages of Access Control Systems
Varieties of Access Control Systems
We provides a selection of sophisticated access control systems to bolster the security of your premises. Whether you seek convenience, high security, or integration with current systems, we have the ideal solution for you.
We offer all these types of access control systems. Upgrade yours today!
Key Elements of Access Control Systems
Implementing Access Control Systems
Deploying access control systems involves several steps, including planning and design, installation, and integration with other security systems. It is crucial to evaluate the security requirements of the facility and select the appropriate type of access control system accordingly.
Why Opt for SECOM Malaysia?
SECOM is a premier provider of security solutions, renowned for its innovative approach and dedication to customer satisfaction. With SECOM’s access control systems, you can:
In summary, access control systems play a vital role in enhancing security and operational efficiency across various industries. By implementing these systems, organizations can better safeguard their assets, streamline access management, and improve their overall security stance.
Boosting Retail Safety with Advanced Access Control Systems
Retail businesses thrive on efficient operations, well-trained staff, and a secure environment to protect assets and maintain customer trust. While CCTV and alarm systems are fundamental to many security setups, an Access Control System adds a crucial layer by managing who can enter specific areas within a store.
In this article, we delve into how access control systems work and how they bolster retail safety, enhance staff accountability, and support daily operations for retail businesses.
What Is an Access Control System?
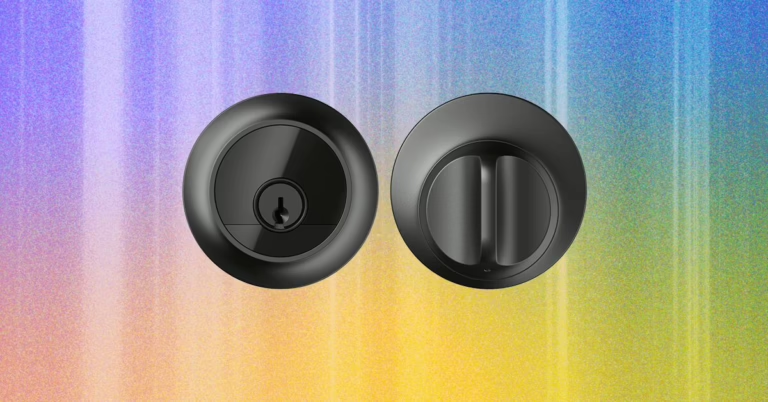
An Access Control System is a cutting-edge security solution that regulates entry to designated zones within your store. Unlike traditional keys—which can be lost, copied, or misused—these systems use digital credentials such as RFID cards, PIN codes, biometric scans, or mobile access.
When integrated with technologies like alarm systems and IP CCTV cameras, access control provides real-time monitoring and greater command over your retail environment, helping to reduce risks and prevent unauthorized access.
Key Ways Access Control Enhances Retail Safety
Prevents Unauthorized Entry
Retailers can assign access rights to specific employees based on their roles or shifts. This limits entry to high-risk areas such as:
- Cash rooms
- Inventory storage areas
- Staff-only corridors or exits
- Server and equipment rooms
This prevents unauthorized personnel, including visitors, contractors, or off-duty staff, from entering sensitive areas.
Improves Staff Accountability
Each employee’s access activity is logged and timestamped. This allows store managers to:
- Monitor movement in restricted areas
- Detect unusual or after-hours access
- Investigate stock discrepancies with audit logs
Over time, having access control can foster a culture of accountability while reducing opportunities for internal theft or carelessness.
Supports Emergency Situations
Access control systems can be configured for emergency responses:
- Lockdown functionality during theft or robbery
- Automatic door release during fire alarms or evacuations
- Temporary access permissions for emergency services
These automated features enhance both safety and compliance during crisis events.
Centralized Management for Multiple Outlets
Retailers with more than one store location can manage access centrally:
- Set and update access rules across all outlets
- Revoke access instantly when staff leave
- Generate reports for security audits
Centralized control ensures consistent policies and reduces manual work, especially during staff turnover or seasonal hiring.
Why Retailers in Malaysia Are Adopting Access Control
Access control has become an essential tool in modern retail security. Here is how it helps address common challenges faced by retail businesses:
| Retail Challenge | Access Control Benefit |
|---|---|
| Unsecured storage areas | Restricts access to authorized personnel only |
| Internal theft or pilferage | Tracks access history for audits and investigations |
| Frequent staff turnover | Credentials can be updated or revoked instantly |
| Multi-store operations | Centralized control over staff access across locations |
| Safety in emergencies | Automated lockdown or door release functions |
How to Choose the Right Access Control System
When selecting a system for your retail store, consider the following factors:
- Number of access points and users: Small shops may need basic card systems, while supermarkets may require multi-zone access.
- Credential types: Choose between RFID cards, PIN codes, biometrics, or mobile-based access.
- Compatibility: Ensure your access control system integrates seamlessly with your existing security infrastructure, such as CCTV, alarm systems, or other intrusion detection solutions.
- Ease of use: A user-friendly interface makes it easier for managers to assign access and generate reports.
- Scalability: Your system should grow with your business, especially if you’re expanding across Malaysia.
- Support and maintenance: Work with an experienced security provider that offers reliable installation and post-sale service.
Build a Safer, More Controlled Retail Space
From limiting access to sensitive areas to tracking staff movements and enabling quick response during emergencies, an Access Control System provides a smart, scalable approach to retail safety. By putting control back into the hands of store owners and managers, it helps create a safer, more organized retail environment built on trust, accountability, and efficiency.
Advantages of Card Access Systems
Card access system, in which card reader devices are used to enter and exit a place, is a security and control system. These systems; It is especially preferred in places where there are many people such as workplaces, schools, hospitals, hotels and shopping malls. Thanks to the card access system, data such as the identity information of people entering and leaving the place, entry and exit times, and the doors they enter and exit can be recorded and reported. Thus, both security and personnel attendance control are ensured. The card access system, which has a very wide usage area, offers great convenience, especially for personnel entry and exit tracking. The system, which is used in many different areas from factories to schools, from public institutions to municipalities and holdings, is preferred as one of the most practical solutions for personnel control.
What is an RFID Reader?
RFID reader means that the recorded value on the card is identified by radio frequency. It is used in many areas today RFID card reader access systemsit offers many advantages to companies in terms of time and costs. For example, the contactless card or credit card feature that we encounter in the financial sector and financial transactions works through RFID technology. This application is also used in the card pass system.
How Does RFID Card Access System Work?
Card access systems developed according to the latest technology and needs are effective control and security systems that can be used in holdings, offices, plazas and facilities. These systems can be used in the following ways in summary:
Card and encrypted personnel can be tracked with card readers offered for sale by Özgür Zaman with the above features. The system, which can also be used for turnstile and door control scenarios, is also effective in increasing security with online data transfer. In addition, since card and camera terminals function to detect people who scan cards, they provide guidance on whether the person who scans the card is the right person.
Advantages of Using Card Door Access Systems
There are many advantages of using a card pass system for institutions and organizations. We can count some of them as follows:
How to Install a Card Access System?
In order to install a card access system in businesses, the physical features, needs and budget of the place must first be taken into consideration. Then, the appropriate card reader, card and central system should be selected and installed. Installation should be done by an expert team. During installation, it is important to place card readers in the right places, lay cables safely, and integrate software and hardware systems and test them. In addition, card access systems must be maintained regularly and updated periodically.
As we mentioned above, the system, which is ideal for using authorized transfer, is also equipped to calculate personnel payroll. It is a special system preferred in almost all businesses, especially in buildings with many doors, in order to implement the scenario through which personnel can enter and from which they cannot. Card access systems are also developed in different technologies for their intended use. In this process, as Özgür Time Control Systems, we offer professional solutions for security and personnel entry and exit control with card reader systems for various usage purposes. You can also contact us to get information about the process.
Can an RFID Card Be Copied?
Copying RFID cards is possible by copying RFID chips. However, this process requires special equipment and technical knowledge. RFID technology is a form of wireless communication used to identify and track objects remotely. This technology provides security and efficiency in many areas, from shopping malls to airports.
RFID cards contain integrated circuits that store personal information and can communicate with the relevant system by scanning it by a specific reader. Copying of these cards can be done using special RFID printers or cloners. These devices can read the information on the card and transfer it to a new card. However, due to security measures, cards are often reinforced with various encryption and protection mechanisms, especially in sensitive areas such as banking and personal authentication. Therefore, copying RFID cards within the scope of the card access system is considered an illegal activity.
What is the Difference Between RFID and NFC?
RFID is a technology that enables the identification of objects using radio waves. an RFID reader is an indispensable device of RFID technology, which has one or more antennas that emit radio waves and receive signals from RFID tags. NFC (Near Field Communication) is a technology that allows two devices to transfer data wirelessly when they are very close to each other (usually a few centimeters). NFC technology is a technology similar to RFID technology. Therefore, it can be used as an RFID reader in NFC devices or NFC card access systems.
How to Ensure Security with Card Access System?
In addition to registered personnel, visitors to the company, company or facility are given cards when they enter areas where security systems are located. Thanks to these cards, visitors can be tracked by security guards. Visitors can switch by having readers read their cards at crossing points. This information is recorded through a special program. Details such as which areas visitors can enter and how long they can stay in relevant areas can be determined in the program.
Thanks to the systems, the necessary permissions for entering and exiting secure areas are provided. All cards given have their own password or algorithm. Thanks to this encrypted pass system, the card is prevented from falling into someone else’s hands. In addition, thanks to the card access system, access to prohibited places, theft and access control of unauthorized persons to some places can be easily carried out.
What are the card types used in card access systems?
In card access systems, cards with magnetic stripes, chips (smart) and RFID basis are generally used. In some systems, contactless (proximity) cards or NFC-enabled devices may also be preferred. Disposable visitor cards or permanent staff cards can be defined depending on the area of use.
Can the card access system be integrated into the existing security infrastructure?
Yes. Modern card access systems can work integrated with existing security cameras, turnstile systems, alarm systems or building automation infrastructures. In this way, both physical security and digital access control can be managed from a single center.
How does the card access system ensure data security?
Card data in the system is usually stored in encrypted form. Additionally, each card has its own unique identification number. In this way, unauthorized access or copying attempts are prevented. Regular software updates and access authorizations also increase data security.
How long does it take to install a card access system?
Installation time varies depending on the scope of the system and building infrastructure. While it can be completed in a few days in small offices, it can take up to several weeks in multi-door or integrated systems. Professional assembly and testing process is important for the smooth operation of the system.