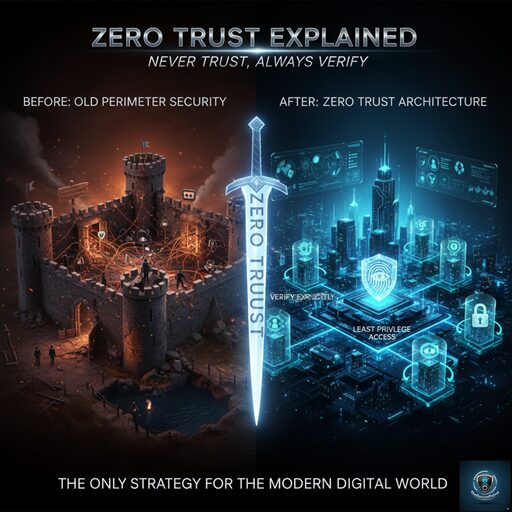
For decades, cybersecurity operated on a simple principle: build a strong wall (firewall) around your network, and trust everyone and everything inside that wall. This “castle-and-moat” model was adequate for a time when employees were strictly contained within physical office buildings.
Today, that model is fatally obsolete. With the rise of hybrid and fully remote workforces, the “castle” has fractured into hundreds of remote homes, coffee shops, and unmanaged personal devices. The network perimeter is dead.
The only sustainable strategy for securing the modern enterprise is Zero Trust Explained. This paradigm shift dictates that security should never be based on location but on continuous, rigorous verification. If you operate a hybrid workforce, understanding Zero Trust Explained is not optional—it is the imperative for survival.
1. The Failure of the Old Model: Why the Firewall is Not Enough
The traditional security model assumes inherent trust once a user is inside the network perimeter. If an attacker bypasses the firewall (say, via a successful phishing attack on a remote employee), they gain near-unrestricted lateral access to servers, databases, and critical applications.
The shift to hybrid work accelerated this collapse:
- Blurred Lines: Company data now resides on personal laptops accessing unsecured home Wi-Fi networks.
- Insider Threats: An authenticated user’s device, if compromised, is treated as fully trustworthy, allowing malware to spread unchecked.
- IoT Expansion: Every personal device (smartwatch, tablet) connected to a home network becomes a potential entry point into the corporate environment.
Because the traditional perimeter failed to protect this decentralized landscape, a new, adaptive model became necessary. This is precisely why Zero Trust Explained rose to prominence.
2. Zero Trust Explained: The Core Principles
At its heart, Zero Trust Explained is a philosophy formalized by standards bodies like NIST and CISA. It operates on the guiding philosophy: Never Trust, Always Verify. Every access request, regardless of where it originates or who is asking, must be treated as hostile until proven otherwise.
The entire framework of Zero Trust Explained is built upon three pillars:
A. Verify Explicitly
Every user, every device, and every application must be authenticated and authorized before granting access. This verification must go beyond a simple username and password, requiring multi-factor authentication (MFA), device posture assessment (is the antivirus running? is the OS patched?), and contextual details (location, time of day).
B. Use Least Privilege Access (LPA)
Instead of granting broad access upon entry, access should be limited to the bare minimum resources required for a specific task. If a marketing manager only needs access to the CRM, they should not be able to access the financial ledger. This microsegmentation prevents an attacker who breaches one area from moving freely across the entire network.
C. Assume Breach
Security architects must plan as if a breach has already occurred or is imminent. This mindset shifts the focus from simple prevention to detection and rapid response. Continuous monitoring, microsegmentation, and rigorous logging are essential components of Zero Trust Explained under this assumption.
3. The Imperative for Hybrid Workforces
The hybrid workforce is the perfect use case for Zero Trust Explained. When employees connect from outside the traditional network, the security model must travel with the data and the user.
Securing Unmanaged Devices
Remote workers often use personal devices (BYOD). Zero Trust Explained addresses this by applying strict checks to the device itself. If a personal laptop running an outdated operating system tries to access a sensitive database, the access is automatically denied, regardless of the user’s credentials.
Mitigating Lateral Movement
If a remote employee’s computer is compromised via a phishing email, Zero Trust Explained prevents that compromised device from spreading malware to other internal systems. Because access is segmented, the malware is contained to the specific, limited resources the employee was authorized to use. This containment is crucial in hybrid environments where IT visibility is often lacking.
Contextual and Adaptive Access
In a hybrid setting, a CFO logging in from the office might be granted full access. The same CFO logging in from an unknown IP address in a foreign country at 3:00 AM might be challenged with additional MFA steps or denied access entirely. Zero Trust Explained makes security adaptive, basing decisions on real-time context.
4. Implementing Zero Trust Explained: Practical Steps
Implementing a comprehensive Zero Trust Explained strategy is a multi-year journey, not a single product installation. Key technologies include:
- Strong Multi-Factor Authentication (MFA): Mandatory MFA is the baseline for all users and accounts.
- Microsegmentation: Breaking the network into small, secure zones where traffic between zones is strictly controlled.
- Software-Defined Perimeter (SDP): Creating secure, individualized connections between the user and the specific application they need, without giving them access to the rest of the network.
- Continuous Monitoring: Utilizing advanced analytics (AI/ML) to track user behavior and detect anomalies instantly. If a user suddenly downloads an unusually large volume of data, access is revoked automatically.
Conclusion
The debate over traditional perimeter security versus Zero Trust Explained is settled. For the dynamic, decentralized reality of the hybrid workforce, the old model is a guaranteed path to compromise.
Zero Trust Explained is more than just a security framework; it is a philosophy that acknowledges the vulnerabilities inherent in modern connectivity. By adopting the mantra “Trust No One,” verifying every request explicitly, and building security around the assets themselves rather than a fragile perimeter, organizations can finally establish resilience in the face of inevitable threats. The time to understand and implement Zero Trust Explained is now.