Understanding Cyber Threat Classifications and Terminologies
Cyber Threat Classifications – Your corporate network is always facing security threats that can manifest in various forms. It is crucial to limit these threats and take necessary measures. There are different ways to classify threats to your system. Cyber threats can be categorized based on the damage they cause, the skill level required to execute the attack, or the motivation behind the attack. We can classify the attacks we encounter based on their intended goals or causes. Based on this philosophy, we can categorize cyber attacks into three main classes:
Cyber Breaches
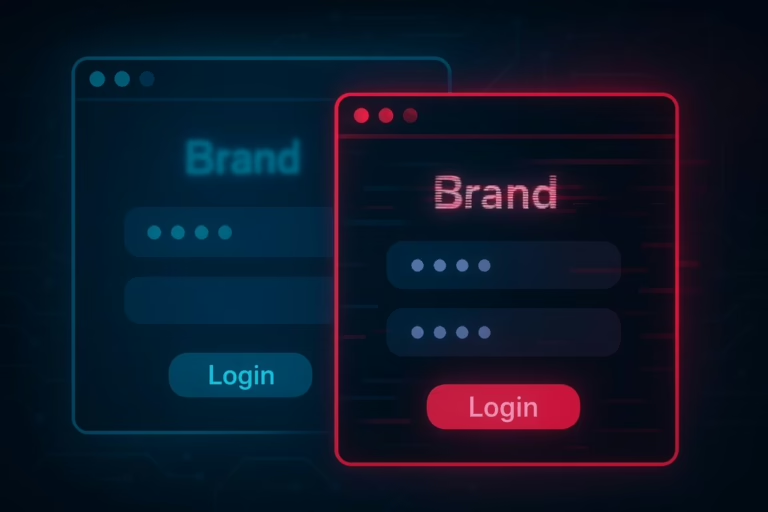
Cyber breaches involve unauthorized access to a system with the intent to compromise cybersecurity. This attack group includes attempts to gain unauthorized access to your system, which is often the first step hackers take. These attacks are designed to infiltrate systems without permission.
Blockage
The second category of attacks is blockage, which includes cyber attacks designed to prevent legitimate access to a system. Blockage attacks typically involve Distributed Denial of Service (DDoS) attacks. The goal of these attacks is not to infiltrate your system but to prevent authorized users from accessing it, thereby disrupting organizational operations.
Malware
The third threat category involves the infiltration of malicious software into a system. Malware includes cyber attacks that involve gaining access to the system or using harmful code. This category encompasses virus attacks, Trojan horses, and spyware. Malware is the most common threat to electronic systems, including home user systems, small networks, and large corporate wide area networks. One reason for this is that malware is designed to spread on its own without the direct involvement of its creator.
The most prominent example of malware is computer viruses. A virus can be generally defined as malware that can modify, delete, damage, or infect other programs with a developed copy of itself. A computer virus is designed similarly to a biological virus, with its primary action being to replicate and spread. The most common method of spreading a virus is by using the victim’s email account to send the virus to everyone in the address book.
Some viruses do not harm the system they infect, but all can cause network slowdowns or interruptions due to the heavy network traffic caused by virus replication. Another type of malware closely related to viruses is Trojan horses. The term is derived from ancient stories. Trojan horses in malware use the same method and are therefore called Trojan horses. They often appear to be useful software, such as an antivirus that cleans your computer, an application that boosts performance, or free software that fixes errors. However, they secretly download a virus or other type of malware onto your computer. While appearing to help you, they can open a backdoor for a cyber attacker by running their malicious code in the background.
Trojan horses are much more likely to be found in illegal software. There are many places on the internet where you can obtain pirated copies of commercial software. Many software programs offered for free under the guise of being cracked or full versions contain Trojan horses. Viruses and Trojan horses are the two most commonly encountered forms of malware. A third category of malware is the rapidly increasing spyware.
Spyware, when it infects your computer, can send all your data to hackers with the intent of full espionage. They particularly have capabilities such as stealing sensitive data, recording videos, and recording audio. Another type of spyware is keyloggers, which record all your keystrokes and send them to hackers. Some can even take periodic screenshots of your computer, especially while you are conducting banking transactions.
Cyber Attacks
Cyber attacks differ from attacks that prevent users from accessing the system (blockage) or those that focus on a specific target like viruses and worms (malware). Cyber attacks are designed to access a specific target system with the aim of gaining unauthorized access. Once this access is achieved, systems can be exploited by malicious hackers. These attacks are generally designed to exploit operating system vulnerabilities, application vulnerabilities, or other security breaches.
Using security vulnerabilities is not the only way to gain unauthorized access to a system. In fact, some methods can be technologically easier to implement. For example, you can exploit human errors to compromise a system’s security. We define such cyber attacks as social engineering attacks. Social engineering is one of the oldest and most effective methods in internet history and was frequently used by Kevin Mitnick. Social engineering uses techniques designed to gather the necessary information to access the target system.
Using social engineering and software vulnerabilities is not the only way to conduct cyber attack attacks. The increasing popularity of wireless networks has led to new types of cyber attacks. Many people are unaware that wireless network signals can often extend up to 100 meters. It is possible to access your internal network by attacking WiFi signals from outside your home or organization.
DDoS Attacks
As the third category of attacks, we can list Denial of Service attacks. Known as DoS or DDoS, these attacks are based on preventing access. In this type of attack, the attacker does not actually access the system but prevents legitimate users from accessing it. It is a commonly used blockage method that fills the targeted system with connection requests to the point where it cannot respond to legitimate requests. DoS and DDoS attacks are extremely common attack methods in today’s technology world.
Cybersecurity Terminology
Security professionals have specific terminology. Individuals with experience in network management or system administrators are likely…