Strengthening Your Team: The Ultimate Guide to Building a Human Firewall
Strengthening Your Team: The Ultimate Guide to Building a Human Firewall
As work environments evolve, cybercriminals find new opportunities to compromise company systems and networks. The shift to remote work has compelled business owners to adapt, implementing technical measures to ensure remote productivity and security. While technical controls are crucial for protecting company data, they are not enough. Employees must be fully trained in cybersecurity skills to protect themselves and their businesses effectively. This article explores the various areas of awareness training required to build a strong, confident, productive, and effective human firewall among your employees.
Understanding Insider Threats
When people hear the term ‘insider threat,’ they often think of disgruntled employees seeking revenge. However, it’s essential to understand that insider threats aren’t always malicious. Accidental insider threats occur when employees make unintentional mistakes that harm the business. Well-intentioned employees might perform legitimate but dangerous actions, such as clicking on malicious links, not following policies and procedures, or responding to phishing emails as if they were legitimate requests.
According to the Ponemon Institute, these accidental threats account for 62% of all insider-related incidents. Whether they realize it or not, employees pose a risk to the security of company networks and the data they hold. A study by Fortinet showed that businesses see phishing attacks (38%) as the top cause of accidental insider threats, followed by spear-phishing (21%), poor passwords (16%), and browsing suspicious or malicious websites (7%).
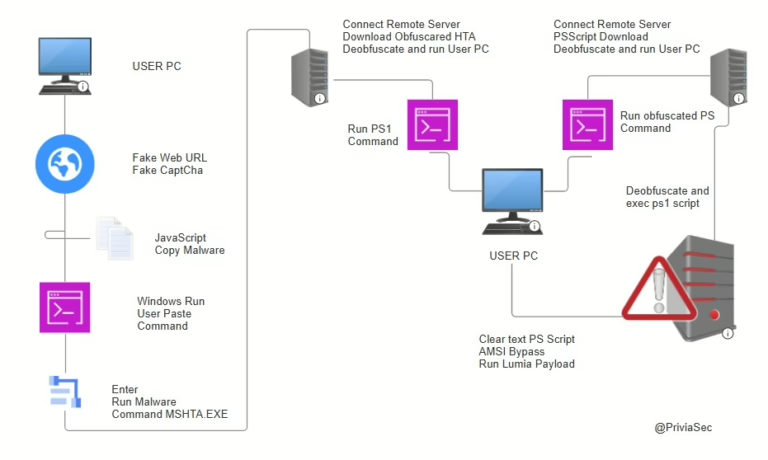
These activities open the door to cybercriminals simply by clicking a link, downloading a file, or responding to a fake phishing request. Educate your employees to take the time to determine whether a request or action is safe and legitimate. These threats must be mitigated not just through technical controls but also by building a better human firewall through awareness training.
Creating a Cyber-Aware Culture
Establishing a cyber-aware culture is essential. Everyone, from executives to the shipping department, has a role to play. If employees see something suspicious, they should say something. However, employees need proper training to understand when and why something might be suspicious and to whom they should report such incidents. Employees must understand how they can contribute to effective cybersecurity strategies rather than relying solely on IT personnel to fix all issues.
Employee Awareness Training
Given that employees can be the best line of defense, it is crucial for small and medium-sized businesses (SMBs) to protect their organizations by including employee education and awareness training as a key component of their overall cybersecurity strategy. By embracing this technique, SMBs can ensure their workforce is prepared to face common and emerging threats.
Training staff on spotting and avoiding phishing attacks, social engineering, ransomware, two-factor authentication requirements, Wi-Fi insecurities, and other threats greatly reduces the chances of falling victim to hackers. Choose a training system that is flexible, allowing you to pivot quickly and train your team on emerging threats, such as phishing attacks claiming you must complete a contact tracing form, which was common in 2020 due to COVID-19.
Setting Policies
Businesses should also review their governance policies. Policies are a great way to keep staff informed and accountable to company expectations regarding behaviors and technology usage. Consider adopting the following four foundational governance policies if you haven’t already:
- A password policy
- An acceptable use policy
- An information handling policy
- A written information security policy (WISP)
Together, these four governing policies provide a sound foundation upon which to mature your cybersecurity program. Training and governance are key to protecting your company. Train employees on attacks and the policies that govern their behaviors. However, most cybersecurity professionals will tell you that you must back these measures up with strong technical protections for when employees forget their training and governance and click on that phishing attack email.
Technical Counter-Measures
While humans can be one of the best firewalls, they are fallible and make mistakes. In such cases, technical measures can be a powerful safeguard to assist users and businesses in staying secure and compromise-free. Two of the most significant and effective technical protections available today include Two-Factor Authentication and Password Managers. Both provide strong technical countermeasures to the attacks we all face today.
Two-Factor Authentication
Two-Factor Authentication (2FA) combines two of the following three identification factors:
- Something you know – Most often a password for your account.
- Something you have – Such as a cell phone with a temporary authentication code.
- Something you are – Such as your fingerprint or facial recognition.
Using two of these three identification factors is the best way to protect your critical accounts. Hackers rely on employees reusing their passwords. They visit dark web forums to find exposed passwords for employees in your internet domain and then attempt to log into accounts (VPN, O365, SaaS solutions) protected by only a username and password. When they see online services protected by 2FA, they often move on to easier targets because they know they may not be able to penetrate such protections.
Unfortunately, many applications today do not yet integrate with two-factor authentication and are at the mercy of employee password hygiene. The fastest way to educate and improve your overall password hygiene at your business is to adopt a password manager. These tools generate secure random passwords, take the guesswork out of logging into online applications, and even improve efficiency by launching websites and automatically logging people in once they have authenticated using 2FA into the password manager.
Password Managers
Cybersecurity professionals recommend using strong, unique, and long (14 or more characters) passwords for every account. The average person can only remember 3 to 4 strong, long, unique passwords. Diligent and creative individuals, using mnemonic memorization techniques, can learn 10 to 15 unique strong and long passphrases.
Password managers can help by generating and storing complex passwords, making it easier for employees to maintain good password hygiene without the burden of remembering multiple strong passwords.
For more information on cybersecurity best practices, visit the Cybersecurity and Infrastructure Security Agency website.