Retail Data Breaches: Essential Cybersecurity Insights for the Holiday Season
The Holiday Season: A Prime Time for Retail and Cyber Threats
As the holiday season kicks into high gear, the retail world prepares for a surge of activity. With a robust economy, shoppers are ready to snag seasonal deals and take advantage of extended shopping hours. But as millions of credit and debit cards get swiped at POS terminals, a critical question arises: Is customer data truly secure? Will post-holiday statements reveal unauthorized charges and mysterious purchases?
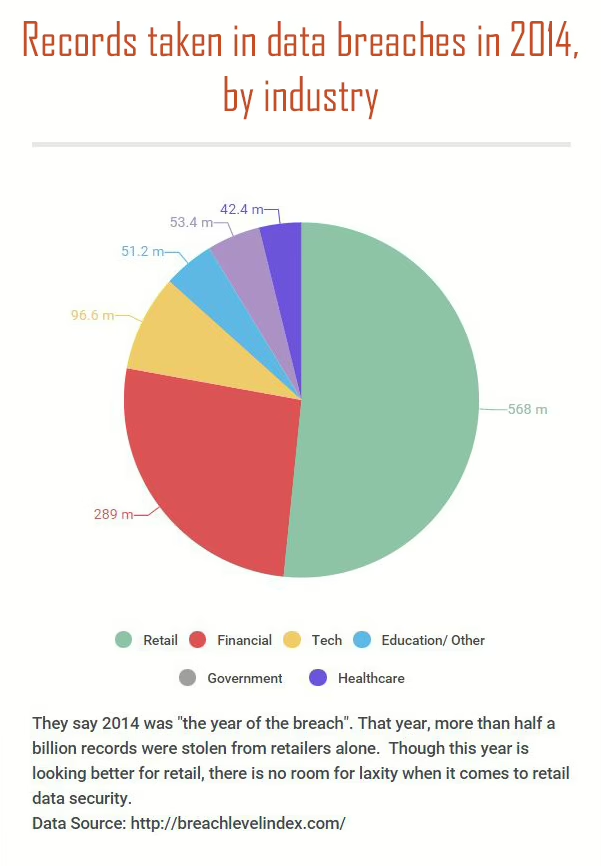
The Growing Threat of Data Breaches
In recent years, data breaches have impacted companies of all sizes. While major breaches involving millions of customers make headlines, the pressing question is: What can be done to secure customer information? Where do vulnerabilities lie, and can we stay ahead of cybercriminals who constantly find ways to bypass security measures?
Cybersecurity experts believe we can hold our own, but only if organizations take serious steps to implement and maintain rigorous, systematic security plans. This requires proper support and funding for IT security teams and making security education an integral part of company culture. It’s time for the C-suite to prioritize data security, given the cost and frequency of data breaches.
Key Lessons from Major Retail Data Breaches
Lesson 1: Thoroughly Vet Your Third-Party Vendors
Investigations into major breaches at retailers like Target and Home Depot revealed that stolen data was sold on the dark web within weeks. The dark web is a hub for criminals to buy and sell credit card information, personally identifiable information (PII), and other illegal goods. Banks and cybercrime experts monitor these forums for signs of compromised customer data.
In both the Target and Home Depot breaches, criminals accessed the networks through third-party vendors. In Target’s case, it was an HVAC company maintaining their refrigerators. The Home Depot breach involved credentials stolen from a third-party vendor. Once inside, criminals exploited a Microsoft Windows vulnerability to upload malicious software designed to steal data from cards swiped at infected POS systems.
Targeting corporate data through vendors is becoming increasingly common. While large corporations can afford robust cybersecurity operations, smaller vendors may struggle with data security. Both corporations and their vendors must ensure that systems containing the personal and financial data of millions of customers are secure. This involves meticulously vetting vendors and ensuring that security protocols are followed.
- Are procedures for granting and removing systems access satisfactory and followed?
- Are security logs routinely monitored to quickly identify attacks or data breaches?
- What password security protocols are in place? Are employees required to change passwords regularly and educated on password security?
- Are Bring-Your-Own-Device policies clear, comprehensive, and enforced?
- Is the connection between networks secure? Can sensitive data be properly encrypted?
- Is the network secure with adequate firewalls, anti-virus, and anti-spam software?
- What is the patching policy? Are frequent patches from major software vendors applied promptly?
Lesson 2: Prioritize Data Protection at All Levels
A report following the eBay attack noted that the company failed to prioritize data protection at all levels. This breach highlighted the need for comprehensive data protection strategies.
The lessons learned from major retail data breaches underscore the importance of robust cybersecurity measures. By vetting third-party vendors and prioritizing data protection at all levels, organizations can better safeguard customer data and mitigate the risks of data breaches.
For further reading on cybersecurity measures, you can visit CISA.