Garmin’s Cybersecurity Crisis: Unpacking the Ransomware Attack and Its Aftermath
If you’re an avid runner or cyclist, you’ve likely heard about the recent Garmin ransomware attack that occurred on July 22nd. This cyber onslaught brought down Garmin’s website, disrupted customer support, disabled apps, and halted communications. Garmin, renowned for its boat radars, GPS systems, and smart fitness watches, is an essential tool for countless athletes tracking their daily exercise routines, including calories burned, steps taken, distance covered, and routes traveled.
The Attack and Its Repercussions
A hacker group known as EvilCorp, based in Russia, breached Garmin’s internal network and encrypted the company’s servers. This attack resulted in a five-day outage, which was later extended to seven days. Many users were left in the lurch as they couldn’t access Garmin Connect applications with their devices. Moreover, users were apprehensive that their personal details, such as geolocation history, might have been stolen from Garmin’s servers.
Garmin’s Response and Security Implications
Garmin stated that they had “obtained the decryption key to recover the files.” This statement raised eyebrows among experts about Garmin’s security practices. It indicated that either the company couldn’t restore its files from backup effectively to thwart the encryption event, or the hackers had critical data they threatened to release publicly, which Garmin couldn’t afford to happen. In either case, it appears that Garmin paid the ransom, which could embolden more attacks on companies in the future.
The Surge of Social Engineering Attacks
Given the nature of the attack, it’s plausible that social engineering techniques were employed. Social engineering involves psychological manipulation to trick users into performing specific actions, often leading to the compromise or theft of critical and sensitive data. These attacks are typically deployed through phishing, where hackers trick users into opening malicious file attachments or clicking links to fake websites, thereby compromising their accounts.
Safeguarding Against Ransomware
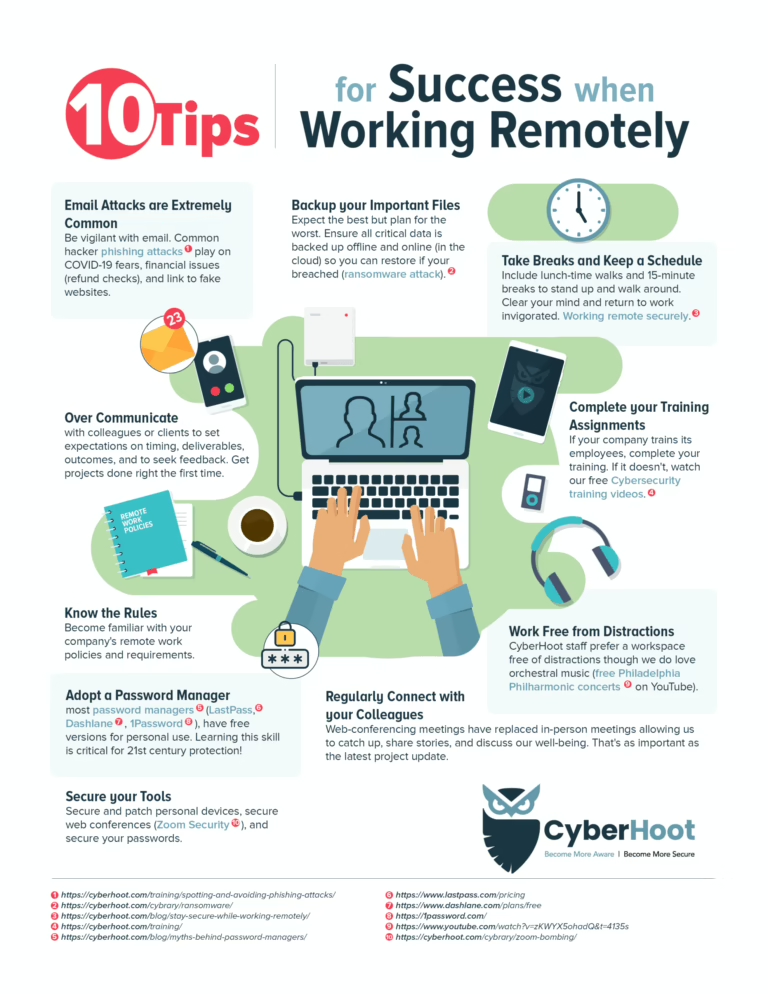
The best defense against most cybersecurity threats is through education and awareness. As Lucy Security CEO Colin Bastable commented, “All the security technology in the world is not going to protect against determined attackers. 97% of losses stem from socially-engineered attacks, and over 90% are initiated by email.” With these statistics in mind, the first step in securing your business is to train your users.
To further prevent ransomware attacks, consider the following actions:
- Adopt two-factor authentication to prevent password breaches of your business’s VPN, email services, and other critical services.
- Regularly back up data following the 3-2-1 backup method for all your critical and sensitive data.
- Train employees on how to spot and avoid phishing attacks, which are the primary way ransomware attacks occur.
- Phish test employees to keep them vigilant about inspecting every email.
- Have a documented and tested Business Continuity and Disaster Recovery (BCDR) plan.
- Ensure your company follows the principle of least privilege.
Understanding WastedLocker Ransomware
Many cybersecurity experts conclude that the ransomware attack was deployed through the malware known as “WastedLocker.” According to experts at Our, WastedLocker is a relatively new ransomware family that has been active for the past few months, targeting high-value entities across various industries. WastedLocker uses a JavaScript-based “SocGholish” toolset to deliver the ransomware payload by masquerading as system or software updates, exploiting UAC bypass techniques to elevate privileges, and leveraging Cobalt Strike for lateral movements.