Malvertising Surge: The Growing Threat of Malicious Ads and How to Stay Safe
The Alarming Resurgence of Malvertising In the ever-changing world of cybersecurity threats, malicious advertisements, commonly known as “malvertising,” have…
Cyber Security

The Alarming Resurgence of Malvertising In the ever-changing world of cybersecurity threats, malicious advertisements, commonly known as “malvertising,” have…
Meterpreter is undoubtedly one of the best tools for cybersecurity experts. In all our tests, studies, and research, we…
JavaScript, as a powerful programming language, inherits properties and functions from its prototypes. However, certain vulnerabilities in JavaScript code…

In a three-tier web architecture, security measures are typically implemented separately at each layer for both internet-facing and local…
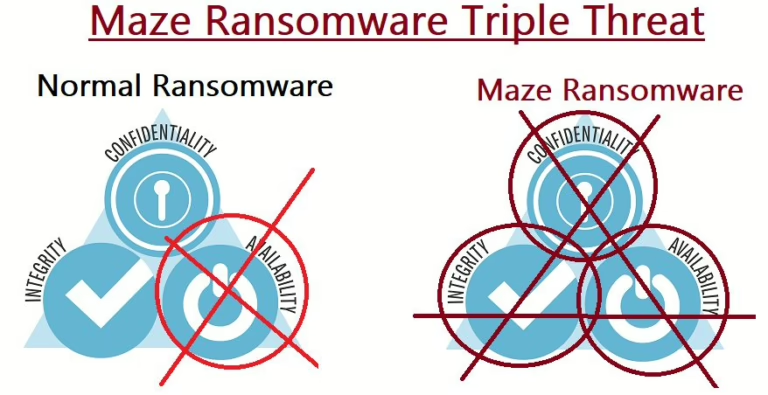
Ransomware has become a favored tool among hacking groups to target companies of all sizes, as seen in the…

Delving into Linux security configuration is indeed a complex and technical subject. This complexity arises from the diversity of…

Linux Firewalls: An Overview Linux operating systems come with a built-in firewall application, much like Windows. Firewall technology has…

DFARS vs CMMC – Security and compliance are of utmost importance, even for unclassified information such as Controlled Unclassified…
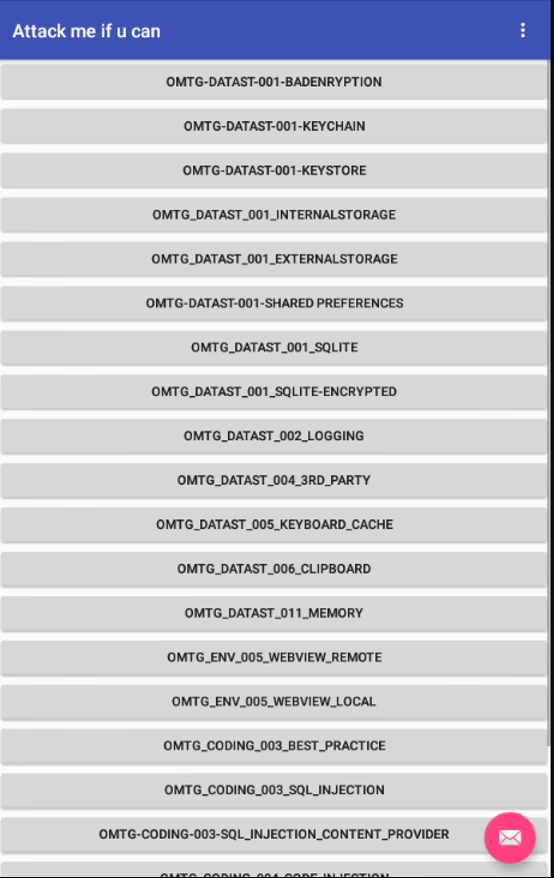
Mobile applications often use the HTTP protocol to communicate with servers. To prevent sensitive data such as session information,…
Let’s face it, how many of us have reset a password at least once this month? For decades, passwords…
End of content
End of content