Ultimate Guide to Locking Down Windows Security Like a Pro
Securing your Windows operating system is a must-do task, whether you’re running Windows 7, 8, 10, or even a…
Cyber Security

Securing your Windows operating system is a must-do task, whether you’re running Windows 7, 8, 10, or even a…

What is a VPN and How Does It Work? A Virtual Private Network, or VPN, is like a secret…
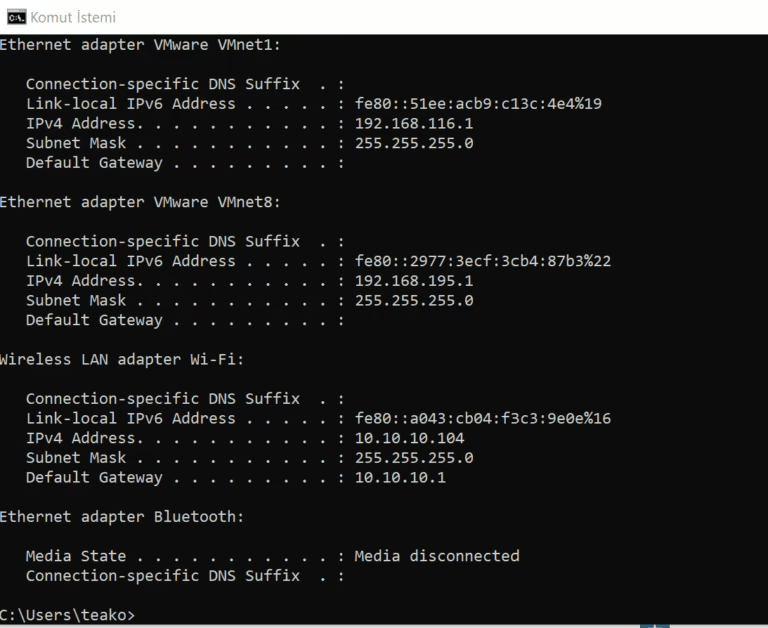
Mastering Network Utilities: A Cybersecurity Essential In the dynamic world of cybersecurity, having a firm grasp on key network…

SYN Flood Attacks: A Deep Dive In today’s digital landscape, SYN Flood attacks pose a serious threat to systems…

EDR, MDR, XDR, and EPP: The Next-Gen Endpoint Security Technologies In today’s digital world, endpoint security technologies like EPP,…

Unleashing the Power of Nmap Welcome to the ultimate guide on Nmap, the network scanning tool that’s a game-changer…

What Are Allow Lists? Allow lists, also known as permit lists, are a powerful cybersecurity tool. They specify trusted…

PCI DSS 4.0: The New Era of Payment Security On March 31, 2022, the Payment Card Industry (PCI) Security…
In the realm of Windows penetration testing, the ultimate aim after breaching a system is to seize control of…
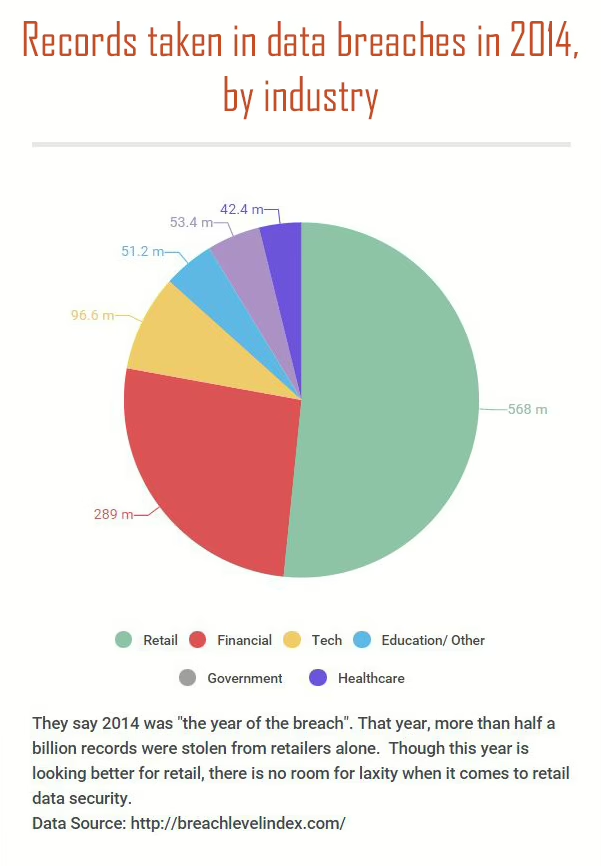
The Holiday Season: A Prime Time for Retail and Cyber Threats As the holiday season kicks into high gear,…
End of content
End of content