Boosting Security with Advanced Keyless Entry Systems – Access control systems
Access control systems are a cornerstone of contemporary security setups, offering keyless entry to protected zones like buildings, rooms, or facilities. These systems employ a variety of technologies to oversee and regulate access, delivering heightened security and convenience.
Understanding Access Control Systems
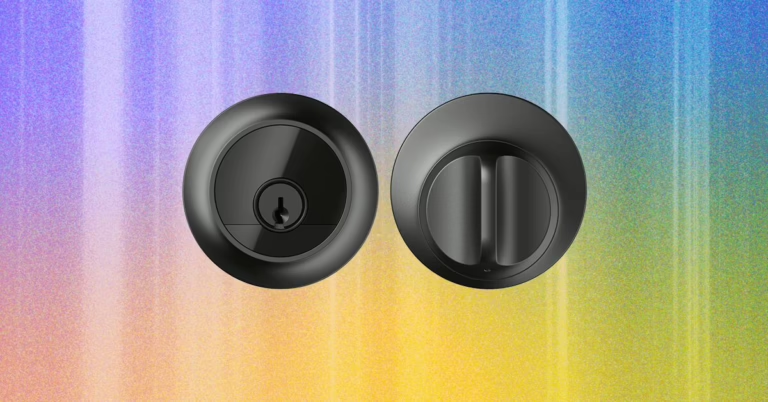
Access control systems are security measures that dictate who can enter or leave a designated area. They utilize a blend of hardware and software to verify users and permit or refuse access based on established criteria. These systems do away with traditional keys, opting instead for electronic credentials like smart cards, smartphones, PIN codes, or biometric data that can recognize fingerprint, vein, face, and iris patterns.
With our’s Access Control Systems, you can be confident that your premises are well-protected. Don’t delay until it’s too late. Assume command of your security now.
Advantages of Access Control Systems
Varieties of Access Control Systems
We provides a selection of sophisticated access control systems to bolster the security of your premises. Whether you seek convenience, high security, or integration with current systems, we have the ideal solution for you.
We offer all these types of access control systems. Upgrade yours today!
Key Elements of Access Control Systems
Implementing Access Control Systems
Deploying access control systems involves several steps, including planning and design, installation, and integration with other security systems. It is crucial to evaluate the security requirements of the facility and select the appropriate type of access control system accordingly.
Why Opt for SECOM Malaysia?
SECOM is a premier provider of security solutions, renowned for its innovative approach and dedication to customer satisfaction. With SECOM’s access control systems, you can:
In summary, access control systems play a vital role in enhancing security and operational efficiency across various industries. By implementing these systems, organizations can better safeguard their assets, streamline access management, and improve their overall security stance.