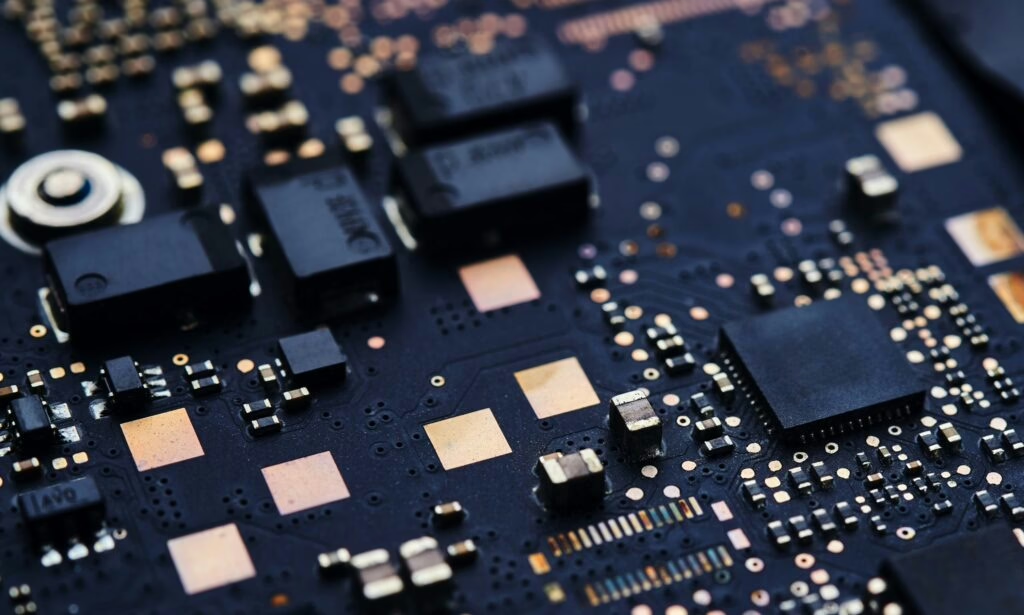
Computer Viruses Uncovered: Types, Spread, and Top Prevention Tips
Computer Viruses: Your Ultimate Guide to Staying Safe
In today’s digital age, understanding computer viruses, their spread, and prevention is crucial. This knowledge empowers you to make informed decisions about protecting your organization with the right virus scanners.
What is a Computer Virus?
We’ve all heard about computer viruses, but what exactly are they? Simply put, a computer virus is a self-replicating program, much like legitimate software such as calculators or paint programs. However, unlike these helpful tools, viruses are designed with malicious intent. They can delete files, alter system settings, and wreak other havoc. The key characteristic of a virus is its ability to self-replicate and spread rapidly, which can lead to issues like excessive network traffic, disrupting organizational networks.
What is a Worm?
A worm is a type of virus that can spread without human intervention. While some sources differentiate between worms and viruses, others consider worms a subset of viruses. Unlike traditional viruses, worms can spread independently without requiring human actions like downloading a file or opening an email attachment. In recent years, worm infections have become more prevalent than traditional viruses. Many of what we commonly refer to as viruses today are actually worms.
How Do Viruses Spread?
The best way to combat viruses is to limit their spread, making it crucial to understand how they propagate. Viruses typically spread through two main methods:
-
Email Address Books
The most common and simplest method is by reading your email address book and sending emails to everyone listed.
-
Network Scanning
The second method involves scanning a network your computer is connected to and copying itself to other accessible machines. This method is more effective but requires more programming skill.
In today’s world, infected computers are often isolated from networks to prevent the spread of viruses. Microsoft Outlook is the most frequently used email program for such virus attacks due to its widespread use, not because of any inherent security flaws.
Another way viruses spread is by scanning the network of the infected system and copying themselves to detected and accessible devices. This type of self-spreading does not require user interaction, which is why programs using this method are classified as worms.
Regardless of how a virus appears, once it enters your system, it will attempt to spread and often cause damage. A virus can do anything that a legitimate program can do once it infects your system, including deleting files, changing system settings, or causing other harm. The threat of virus attacks cannot be overstated. Some new virus strains use advanced technologies that can disable existing security software like antivirus scanners and firewalls.
Notable Viruses
-
Rombertik
Rombertik wreaked havoc in 2015, targeting users of Internet Explorer, Firefox, and Chrome. It was designed to steal secret information and was first announced by researchers at the Cisco Talos Security and Intelligence Group. This malware used the browser to read web sites’ user credentials, copied and sent itself as an email attachment. In some cases, Rombertik wrote itself over the master boot record on the hard drive, preventing the machine from booting and starting to encrypt files in the user’s main directory.
-
Shamoon
Discovered in 2012, Shamoon targeted computers running Microsoft Windows in the energy sector. Also known as W32.DistTrack, it was discovered by Symantec, Kaspersky Lab, and Seculert on August 16, 2012. It is a modular computer virus targeting the last 32-bit NT kernel versions of Microsoft Windows. Shamoon was actually a data theft program targeting systems in energy companies. Another variant of Shamoon reappeared in 2017.
Other notable viruses include Gameover Zeus, Mirai, Linux Encoder 1, Cat RAT, and many more.
Ransomware
While many people first discussed ransomware with the emergence of CryptoLocker in 2013, ransomware had been discovered much earlier. The first known ransomware was the 1989 PC Cyborg Trojan, which only encrypted weakly symmetric encrypted file names. Notably, in early 2017, the WannaCry ransomware caused significant damage to health systems in England. The Bad Rabbit computer virus spread towards the end of 2017, appearing in Russia and Ukraine before quickly spreading worldwide. It was also a type of ransomware.
Types of Viruses
There are many types of viruses, classified either by their method of spread or by their activities on the target computer.
-
Macro Virus
Many office products, including Microsoft Office, allow users to write mini-programs called macros. These macros can also be written as viruses. Macro viruses emerged and infected office documents’ macros. Microsoft Outlook is designed so that a programmer can write scripts using a subset of the Visual Basic programming language called Visual Basic for Applications (VBA). This scripting language is actually built into all Microsoft Office products. Programmers can also use the closely related VBScript language. Both languages are relatively easy to learn. If a script is attached to an email and the recipient uses Outlook, the script can be executed. This execution allows for numerous operations, including scanning the address book, searching for addresses, sending emails, deleting emails, and more. Many organizations have security measures against macro viruses, and today’s office programs disable macros by default.
-
Boot Sector Virus
As the name suggests, a boot sector virus infects the boot sector of a drive instead of the operating system. Most antivirus software struggles to detect or remove viruses in this area because it operates within the operating system.
-
Multipartite Viruses
Multipartite viruses attack computers in various ways. For example, they can infect the boot sector of a hard drive or multiple files.
-
Memory-Resident Viruses
Memory-resident viruses install themselves and hide in RAM from the time the computer boots up until it is shut down. They remain as long as there is electricity in the RAM. Even if you format the disk, they can repeatedly copy themselves from the RAM.
-
Armored Viruses
Armored viruses use techniques to make analysis difficult. Code obfuscation is one such method, where the code is written in a complex manner to hinder analysis. Compressed code is another method used to protect the virus and make analysis challenging.
-
Stealth Viruses
There are several types of stealth viruses. A stealth virus tries to hide itself from antivirus applications, using techniques to conceal itself and spread.
-
Sparse Infector Viruses
Sparse infector viruses perform their malicious activities only occasionally, making them harder to detect.
For more information on computer viruses and how to protect your systems, visit CISA’s website.