Wireless Network Security: Unmasking Threats and Fortifying Defenses
Wireless Network Threats: A Comprehensive Guide
Despite significant advancements in wireless network security, notably the introduction of WPA and WPA2 using CCMP after WEP, vulnerabilities persist. While data frames are now encrypted, management frames remain exposed, leaving networks susceptible to Denial of Service (DoS) attacks.
DoS Attacks on Wireless Networks
Wireless networks face various DoS attacks, some of which are unique to wireless environments. These attacks typically occur at the OSI model’s second layer, where communication happens through frames (Data Link Layer). Additionally, jammers can disrupt communication at the physical layer by distorting signals.
Common attack methods include authentication/association flood and deauthentication/disassociation flood.
The Authentication and Association Process
A client connects to an Access Point (AP) through a series of steps:
- The client sends an authentication request.
- The AP responds with an authentication reply.
- The client sends an association request.
- The AP responds with an association reply.
Authentication is necessary for association. A client can authenticate with multiple systems but can only associate with one AP at a time.
Targeted Attacks
To target a specific user, tools like airodump-ng or Kismet can identify users connected to the target wireless network before initiating an attack. These attacks can temporarily disrupt communication and may require restarting the AP.
Authentication and Deauthentication Attacks
An authentication attack can be launched using a specific command. Deauthentication attacks are relatively simple to execute. Tools like mdk3 can send spoofed frames to a broadcast MAC address, disconnecting all clients from the wireless network.
Association Flood Attacks
An AP maintains a table for each associated client. In an association flood attack, the goal is to fill up the limited memory of this table, preventing new clients from connecting. This is achieved by sending continuous association requests to the AP with constantly changing MAC addresses.
Bypassing MAC Address Filtering
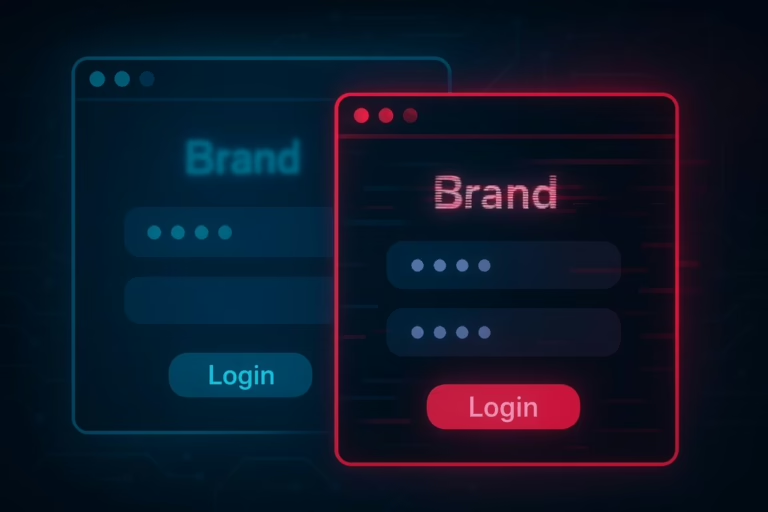
MAC address filtering is a security measure that allows only specified MAC addresses to connect to the wireless network. However, this protection can be bypassed by identifying and cloning the MAC addresses of authorized users.
Using tools like airodump-ng, information about users connected to the target wireless network can be captured. By cloning the MAC address of an authorized user, an attacker can bypass MAC address filtering and connect to the network.
For more detailed information on wireless network security, you can refer to authoritative sources like the US-CERT website.