Unlocking Windows Post-Exploitation: A Deep Dive into Nishang
Nishang, crafted by the skilled Nikhil Mittal, stands as a robust collection of post-exploitation tools. This suite is composed of various PowerShell scripts, each designed to aid in tasks such as port scanning, information gathering, privilege escalation, credential harvesting, and establishing backdoors. Nishang’s strength lies in its ability to evade antivirus detection due to its PowerShell foundation, its seamless compatibility with all Windows operating systems, and its minimal footprint, operating solely in memory without the need for additional installations.
Establishing Backdoors with Nishang
One of the ultimate goals for an attacker during the post-exploitation phase is to maintain persistence within the compromised system. This is achieved by creating a backdoor to ensure continued access. Nishang provides several methods to accomplish this, each with its unique approach.
Add-RegBackdoor
The Add-RegBackdoor script manipulates the Windows registry to create a backdoor. It alters the registry keys associated with the Sticky Keys and Utility Manager executables (sethc.exe and utilman.exe) to run custom payloads. Additionally, it disables Network Level Authentication (NLA) to allow remote payload execution via RDP. The primary parameter for this script is the “Payload” parameter, which specifies the application to be executed on the target system, defaulting to “cmd.exe”.
Add-ScrnSaveBackdoor
The Add-ScrnSaveBackdoor script utilizes the Windows screensaver functionality to execute payloads. It creates a custom screensaver file (Ribbons.scr) in the “C:WindowsSystem32” directory and modifies the registry to ensure the screensaver activates after a period of inactivity. When the screensaver is triggered, it executes the specified payload, which can range from a simple command to a more complex script downloaded from the internet.
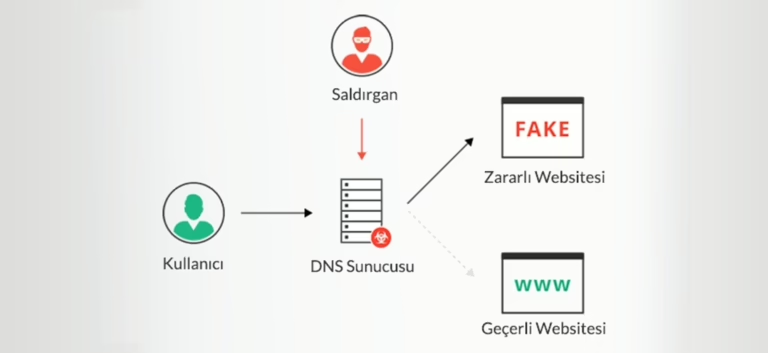
DNS_TXT_Pwnage
The DNS_TXT_Pwnage script employs DNS TXT records to execute payloads and obtain a shell. It continuously queries a DNS server for TXT records, which contain encoded commands. These commands are then decoded and executed on the compromised machine. To use this script, a DNS server with configurable TXT records is required. The script includes parameters such as “StartDomain”, “CommandDomain”, and “AuthNS” to specify the domains and name servers involved in the attack.
Gupt-Backdoor
The Gupt-Backdoor script creates a Wi-Fi access point to execute commands and download scripts on the victim machine. It monitors nearby Wi-Fi networks and uses the “MagicString” parameter to identify target networks. Depending on the configuration, Gupt can execute commands directly or download and execute scripts from a specified URL. The script includes additional parameters such as “Arguments” and “EncodedCmd” to provide flexibility in command execution.
Conclusion
Nishang is a versatile and powerful toolset for post-exploitation activities. Its ability to operate within the constraints of PowerShell and its compatibility with Windows systems make it a valuable asset for security professionals and attackers alike. By understanding and utilizing the various scripts and techniques offered by Nishang, one can effectively maintain persistence and control over compromised systems.