Teen Geniuses Behind the Epic Twitter Bitcoin Scam Caught!
The Epic Twitter Bitcoin Scam
In a jaw-dropping twist, three young whiz kids, aged 17, 19, and 22, have been nabbed for their alleged roles in a high-stakes Bitcoin scam that rocked Twitter on July 15. This scam involved the unprecedented hijacking of verified Twitter accounts belonging to big names like Elon Musk, Jeff Bezos, and Bill Gates, as well as major corporations such as Apple, Binance, and Coinbase.
The Scam Unfolds
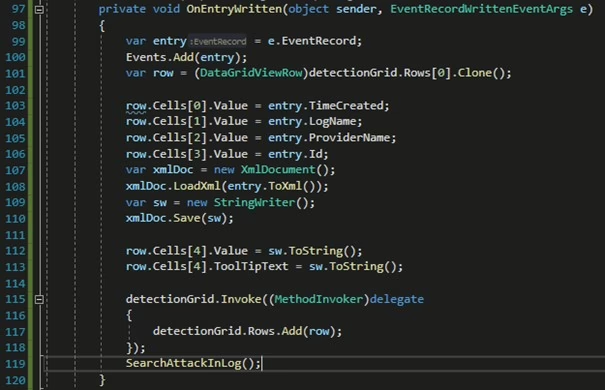
The perpetrators, identified as Mason Sheppard, 19, from the UK, Nima Fazeli, 22, from Florida, and an unnamed juvenile, reportedly gained access to Twitter’s internal systems through targeted attacks on employees. Once inside, they used the compromised accounts to promote a Bitcoin scam, promising to double the amount of Bitcoin sent to them.
According to the U.S. Department of Justice, the trio faces serious charges, including conspiracy, money laundering, and unauthorized access to a protected computer. Graham Clark, the 17-year-old alleged mastermind, is charged with 30 felony counts for using the hijacked accounts to scam hundreds of unsuspecting victims.
Justice for Cybercrimes
U.S. Attorney Anderson made a stern statement, warning cybercriminals that they should not assume anonymity in such high-profile attacks. Twitter has since taken significant measures to restrict access to its systems and has warned users of potential delays in support responses as they work tirelessly to secure their platform.
Emerging Threats: DNS-over-HTTPS Protocol
In related news, Kaspersky has reported that the Oilrig (APT34) hacking group, believed to be based in Iran, has been using the DNS-over-HTTPS protocol to secretly exfiltrate data in cyber attacks. This makes Oilrig the first known Advanced Persistent Threat (APT) group to employ this method.
Malware analyst Vincente Diaz noted that the group uses a tool called DNSExfiltrator, which creates a covert communication channel to exfiltrate data. This tool can transfer files through classic DNS requests, making it exceptionally difficult to detect and track the group’s activities.
Critical Vulnerability Found in Zoom
Security researcher Tom Anthony discovered a critical vulnerability in Zoom’s six-digit password verification system for private meetings. The lack of restrictions on password attempts allowed Anthony to develop a Python script that could crack the password in minutes using a cloud server, potentially enabling unauthorized access to private meetings.
Anthony responsibly reported the issue to Zoom on April 1, 2020, and the company swiftly released a fix on April 9, 2020, demonstrating their commitment to user security.
Microsoft’s Generous Bug Bounty Program
In a positive development, Microsoft awarded a staggering $13.7 million in bug bounties to security researchers over the past year, according to a report from the Microsoft Security Response Center (MSRC). This amount is three times higher than the previous year, reflecting Microsoft’s expanded bug bounty programs for products like Azure, Edge, and Xbox.
The report highlighted that over 300 researchers from six continents submitted reports, leading to the discovery of more than 1,000 valid vulnerabilities. Microsoft has introduced several new bug bounty programs, including those for Microsoft Dynamics 365, Azure Security Lab, Microsoft Edge Chromium, ElectionGuard, Identity, Xbox, Azure Sphere Security, and Windows Insider Preview.
Microsoft expressed sincere gratitude to the security researchers for their invaluable contributions to making Microsoft products more secure.