Ransomware profits drop as victims stop paying hackers
The data is clear: Ransomware profits drop significantly as organizations prioritize resilience over capitulation. For years, the ransomware ecosystem thrived on a simple premise: rapid decryption of systems was worth the cost of the ransom. However, a major shift in corporate policy and technological maturity is finally disrupting this criminal business model. The dramatic decline in the percentage of victims choosing to pay means that the financial incentive driving these attacks is eroding, causing Ransomware profits drop to their lowest levels in years. This trend signifies a critical turning point in the global fight against cyber extortion.
Why Ransomware Profits Drop
Recent reports confirm a steep decline in the percentage of victims who submit to ransom demands. What is driving this decisive shift in strategy against financially motivated cybercrime?
Robust Backup and Recovery Strategies
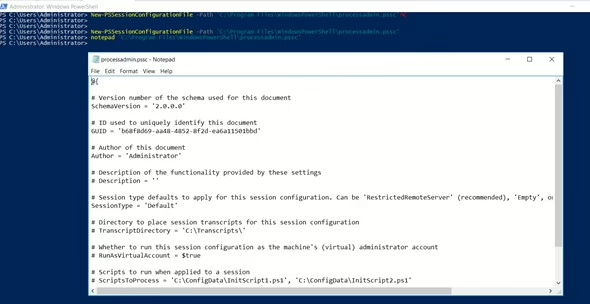
The single biggest factor in the decline of payments is enterprise resilience. Organizations are no longer crippled by file encryption because they have invested heavily in immutable backups and fast recovery processes (RTO/RPO).
Growing Distrust of Ransomware Operators
Victims have become increasingly skeptical of the attackers’ promises. Paying the ransom does not guarantee a clean, working decryption key, and it certainly does not guarantee that stolen data will be deleted.
Legal and Ethical Pressure
Governments and law enforcement agencies globally are applying intense pressure to stop payments, viewing them as funding organized crime and nation-state actors.
The Economic Impact: Quantifying the Decline
While the total number of attacks remains high, the overall financial success of the criminal enterprises is waning.
What This Means for Cyber Defense Strategy
The fact that Ransomware profits drop is a victory for resilience, but it does not mean the fight is over. It validates focusing budgets on prevention and recovery over post-incident response involving ransom.

The refusal to pay is slowly starving the ransomware business model. By maintaining and strengthening their defensive and recovery postures, organizations ensure that the successful trend of falling Ransomware profits drop continues, ultimately making the entire criminal endeavor less profitable and less frequent. The rate at which companies targeted in ransomware attacks are paying ransoms is steadily decreasing. According to recent data, only 23% of companies that suffer a data breach are giving in to the demands of cyber attackers. This decline confirms the general trend that cybersecurity firm Coveware has observed over the past six years, showing that, with some exceptions, the tendency to pay is decreasing.
In the first quarter of 2024, the ransom payment rate was recorded as 28%. Although there was a slight increase in the following period, it fell to an all-time low in the third quarter of 2025. This is considered a result of improvements in companies cybersecurity strategies and increased legal sanctions. As organizations become more aware of the potential fallout from ransomware incidents, they are increasingly investing in robust cybersecurity measures. This includes implementing advanced encryption protocols, conducting regular security audits, and providing employee training on recognizing phishing attempts and other common attack vectors. By fortifying their defenses, companies are not only protecting their data but also reducing their reliance on paying ransoms, which can perpetuate the cycle of cybercrime.
The shift in mindset among companies is also influenced by the growing awareness of the legal implications of making ransom payments. In many jurisdictions, paying a ransom can be seen as aiding and abetting criminal activity, which could lead to severe repercussions for the organizations involved. As a result, companies are weighing the risks of complying with attackers’ demands against the potential for long-term damage to their reputation and financial standing.
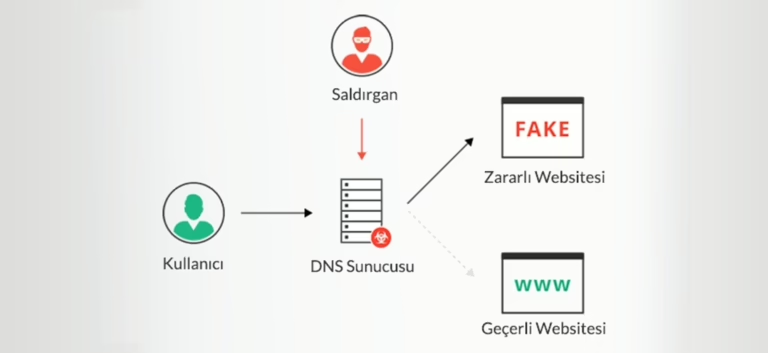
Furthermore, law enforcement agencies and government bodies are actively discouraging ransom payments. Initiatives such as public awareness campaigns and guidelines for victims of ransomware attacks are being launched to inform businesses about the risks associated with paying ransoms. These efforts aim to create a unified front against cybercriminals and to promote resilience within organizations. The decrease in payment rates has also led to a decline in the profits of ransomware groups. According to recent reports, the total revenue generated by ransomware attacks has seen a significant drop, with some estimates suggesting that the earnings of these groups have halved over the past two years. This downturn in profitability is forcing cybercriminals to adapt their tactics, often leading to more aggressive and sophisticated attacks in an attempt to secure payments. One emerging trend among ransomware attackers is the use of double extortion tactics. In this scenario, attackers not only encrypt a victim’s data but also threaten to leak sensitive information if the ransom is not paid. This strategy puts additional pressure on organizations to comply, as the potential for reputational damage can be even greater than the immediate financial loss of losing access to data. Companies are now faced with the difficult decision of whether to risk paying a ransom with no guarantee of data recovery or to invest in preventive measures that could mitigate such threats in the future.
Additionally, the insurance industry is responding to the changing landscape of ransomware attacks. Cyber insurance policies are becoming more stringent, with providers implementing stricter requirements for companies seeking coverage. This includes demonstrating that adequate cybersecurity measures are in place before a policy is issued. These changes are designed to reduce the number of claims resulting from ransomware incidents, ultimately driving organizations to prioritize cybersecurity investments to qualify for coverage. Meanwhile, the cybersecurity community continues to develop innovative solutions to combat ransomware. New tools and technologies are being introduced to help organizations detect and respond to threats more effectively. These advancements include artificial intelligence-driven monitoring systems that can identify suspicious activity in real time, allowing for quicker incident response and mitigation. Additionally, collaboration among cybersecurity professionals is fostering the sharing of intelligence about emerging threats, enabling companies to stay one step ahead of attackers.
The decline in ransom payments marks a significant shift in the battle against ransomware attacks. As companies prioritize cybersecurity and legal frameworks evolve, the profitability of ransomware for cybercriminals is diminishing. This trend not only reflects an increased awareness of the risks associated with paying ransoms but also highlights the importance of investing in preventive measures to protect sensitive data. With continued innovation in cybersecurity and a collective effort to combat cybercrime, the hope is that the tide will turn, leading to a safer digital landscape for businesses and consumers alike.