Ransom DDoS Attacks: How to Protect Your Business and Fight Back
What Are Ransom DDoS Attacks?
A Ransom Distributed Denial of Service (DDoS) attack, or RDDOS, is a cyber shakedown. Criminals threaten to crash your online services unless you pay up. These attacks are on the rise, with hackers often sending ransom notes before or after launching an assault. The goal? To panic you into paying by showing they mean business. Even a few seconds of downtime can cost your organization big time.
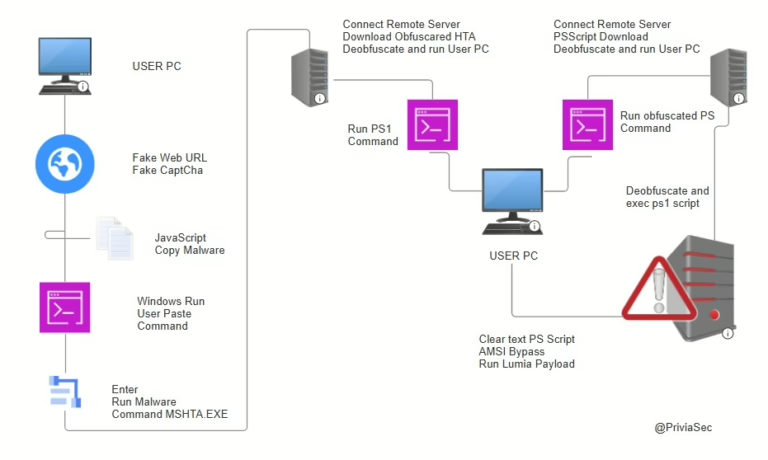
How Ransom DDoS Attacks Work
Most ransom DDoS attacks start with a threat—a ransom note. The attacker warns you of an impending strike, sometimes even launching a small attack to prove they’re serious. This is all about pressure, pushing you to pay up before the real damage begins.
Stages of a Ransom DDoS Attack
- Initial Attack: The hacker starts flooding your network with traffic, usually using botnets. They target weak spots in your system, often at the third, fourth, or seventh layers of the OSI model.
- System Overload: Your servers get slammed with traffic, slowing down or crashing entirely. Sometimes, your network or security devices fail before the servers do.
- Resource Depletion: The attacker keeps draining your system’s resources. Without intervention, your communication stays disrupted. Stopping an ongoing attack is tough, even with measures like rate limiting or IP blocking.
- Ransom Demands: The attacker keeps sending threats and payment demands, trying to squeeze money out of you.
What’s a DDoS Ransom Note?
A DDoS ransom note is a threat sent by cybercriminals. It demands money, often in Bitcoin, and usually comes from a throwaway email address. Sometimes, attackers send multiple messages with detailed demands or even fake advice on how to defend against the attack.
Details of Ransom DDoS Attacks
Ransom notes often claim the attacker can launch massive cyberattacks, like a 3Tbps assault within 24 to 48 hours. But these claims aren’t always true. The attacker might not have the resources or money to pull off such a large-scale attack. They might even lie about being part of a famous hacker group to scare you. While many of these threats are bluffs, there’s always a chance they’re real—and it’s nearly impossible to verify.
Payment Demands and Instructions
Ransom notes usually demand payment in Bitcoin, which helps attackers stay anonymous. They often set a deadline to create urgency and panic, pushing you to pay fast. Some attackers might even negotiate or extend the deadline slightly, but don’t count on it.
To Pay or Not to Pay?
Paying the ransom isn’t always the right move. Some organizations pay quickly, hoping to end the attack. But there’s no guarantee the attack will stop even if you pay. Plus, paying up can make you a target for future attacks, as hackers see you as an easy mark.
Still, many organizations choose to pay when faced with a credible threat, even if the disruption is short. It’s crucial to take all threats seriously and beef up your security. While not all ransom DDoS attacks are legitimate, many succeed. Large-scale attacks require serious resources, which can be expensive. Attackers often cut costs by renting botnet networks on the Dark Web, aiming to hit hard and fast.
How to Protect Against Ransom DDoS Attacks
The best defense is a good offense. Use a DDoS mitigation or protection service. You can get these from Internet Service Providers (ISPs) or specialized companies like Cloudflare, which offer DDoS mitigation and prevention systems.