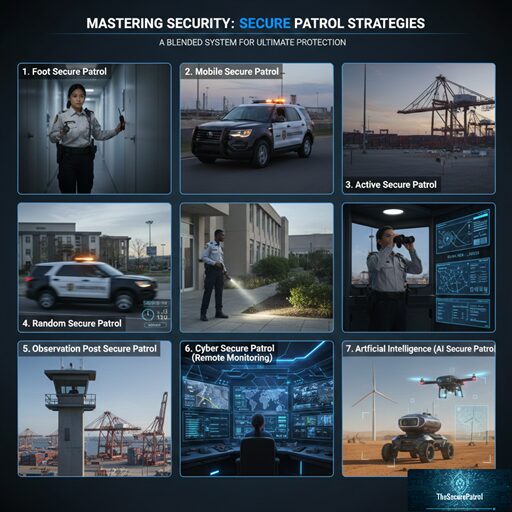
Secure Patrol Strategies
A comprehensive secure patrol strategy is the foundation of effective physical security. It involves the systematic movement of security personnel or technology across a designated area to deter threats, detect anomalies, and respond swiftly to incidents. In today’s complex security landscape, understanding the various methods of implementing a secure patrol is crucial for businesses, institutions, and residential properties looking to maximize protection.