🏰 The 7-Layer Model for Protecting Your Digital Fortress: An Architectural Guide
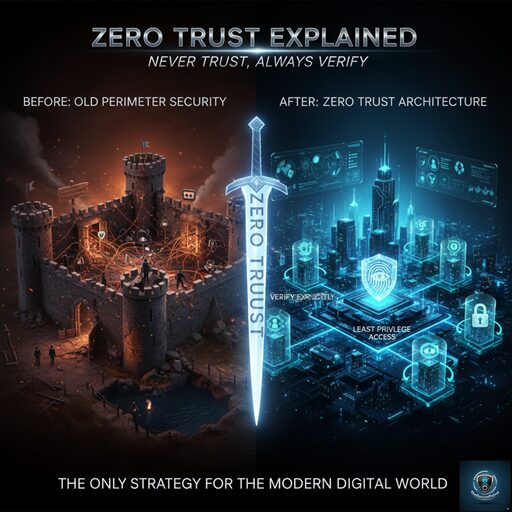
In the dynamic cyber landscape of today, effective security requires a comprehensive, multi-layered strategy. Simply relying on a single firewall or antivirus solution is insufficient for Protecting Your Digital Fortress. Instead, security leaders must adopt an architectural approach—a model that views the organization’s assets as a Digital Fortress requiring defense at every conceivable entry point. This 7-Layer Model for Protecting Your Digital Fortress provides a structured framework for CISOs and security professionals to audit, build, and optimize their defense posture, ensuring robust security from the perimeter to the core.
The Foundation: Why a Layered Approach is Crucial for Protecting Your Digital Fortress
The principle of “Defense in Depth” dictates that failure in one security control should not lead to complete compromise. By implementing seven distinct layers, you create redundancy, ensuring that an attacker who bypasses Layer 1 still faces six additional obstacles before compromising critical assets. This integrated strategy is the key to successfully Protecting Your Digital Fortress.
The 7 Layers for Protecting Your Digital Fortress
Layer 1: The Perimeter (Network Security)
This is the outermost wall of your Digital Fortress. It manages traffic entering and leaving your network.
- Controls: Firewalls (Next-Generation), Intrusion Prevention Systems (IPS), Demilitarized Zones (DMZs), and VPN gateways.
- Goal: To filter malicious traffic and block unauthorized access attempts before they reach the internal environment.
Layer 2: Access & Identity (Authentication)
This layer verifies the legitimacy of users and systems attempting to access resources—a fundamental aspect of Protecting Your Digital Fortress.
- Controls: Multi-Factor Authentication (MFA), Strong Password Policies, Identity and Access Management (IAM) systems, and Single Sign-On (SSO).
- Goal: To ensure that only verified and authorized users can gain entry, minimizing the risk of credential compromise.
Layer 3: Endpoint Protection (Device Security)
This layer focuses on the devices used by employees (laptops, mobile phones, servers), which are frequent targets for initial compromise.
- Controls: Antivirus/Anti-Malware, Endpoint Detection and Response (EDR), Disk Encryption, and Host-based Firewalls.
- Goal: To detect, isolate, and remediate threats that bypass the network perimeter and land on a local device.
Layer 4: Application Security
With increasing use of proprietary and third-party software, this layer protects the code and functionality of applications themselves.
- Controls: Web Application Firewalls (WAFs), Secure Coding Practices, Static and Dynamic Application Security Testing (SAST/DAST), and input validation.
- Goal: To prevent common application vulnerabilities (like SQL injection or XSS) that could be exploited to steal data.
Layer 5: Data Security (The Crown Jewels)
This is perhaps the most critical layer for Protecting Your Digital Fortress as it focuses directly on the assets you are trying to defend: the data itself.
- Controls: Data Loss Prevention (DLP) systems, Data Encryption (at rest and in transit), and stringent data classification policies.
- Goal: To ensure sensitive data cannot be accessed by unauthorized parties and cannot leave the organizational boundaries improperly.
Layer 6: Visibility & Intelligence (Monitoring and Detection)
This layer acts as the eyes and ears inside the Digital Fortress, constantly looking for signs of intrusion or compromise.
- Controls: Security Information and Event Management (SIEM), Threat Intelligence Feeds, Log Management systems, and continuous monitoring.
- Goal: To quickly detect anomalous behavior and alert security teams to threats that have slipped past the outer defenses.
Layer 7: Human Factor (Awareness and Training)
Often cited as the weakest link, the human layer is vital for Protecting Your Digital Fortress.
- Controls: Regular Security Awareness Training, Phishing Simulations, and clear Incident Response protocols.
- Goal: To educate personnel on security policies and empower them to recognize and report social engineering attempts and physical security lapses.
Architectural Success in Protecting Your Digital Fortress
The power of this 7-Layer Model for Protecting Your Digital Fortress lies in its synergy. Alerts from the Data Layer (L5) might be cross-referenced with logs from the Visibility Layer (L6), confirming a perimeter breach that was initially missed by the Network Layer (L1). By implementing robust controls across all seven layers, organizations achieve true Defense in Depth, making the cost and effort of attack prohibitively high for cybercriminals.
In today’s hyper-connected world, data isn’t just important; it’s the new currency. It’s the lifeblood of your business, the core of your operations, and the foundation of your customer relationships. And where does this digital gold reside? In a data center.
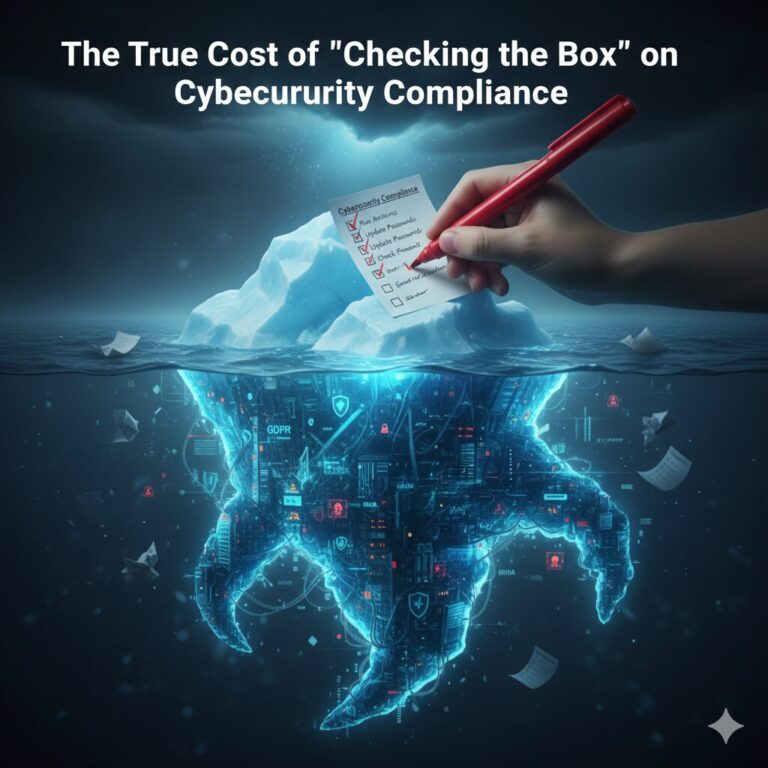
But with this immense value comes immense risk. Data centers are high-priority targets for everyone from sophisticated cybercriminals to physical intruders. A single breach can be catastrophic, leading to devastating financial losses, regulatory fines, and irreparable damage to your reputation.
So, how do you protect this digital fortress? A single padlock or one strong firewall won’t cut it. The solution is a comprehensive, layered security approach. Think of it like a medieval castle: you don’t just have one high wall. You have a moat, an outer wall, an inner wall, towers, and guards, all working together.
This “defense-in-depth” strategy is the core of the 7-layer data center security model. Let’s break down each layer, from the outside in.
Layer 1: The Perimeter (Site Property)
This is your first line of defense. It’s all about securing the physical land your facility sits on, long before anyone can touch the building.
- What it is: Physical barriers like high-security fencing, vehicle crash barriers (bollards), and clear demarcation of property lines.
- Why it matters: It deters casual trespassers and provides a critical “buffer zone.” This layer is monitored by 24/7 security patrol services and comprehensive video surveillance (CCTV) to detect potential threats early.
Layer 2: The Facility (Building Shell)
Once past the perimeter, an intruder faces the building itself. This layer focuses on making the structure a “hard target.”
- What it is: Reinforced walls, secure (and minimal) entry points, bullet-resistant glass, and strictly controlled access doors.
- Why it matters: This layer controls all traffic into the building. Access isn’t granted with just a simple key. It requires verified credentials, managed through a central data center access control system, often reviewed by on-site security personnel.
Layer 3: The “White Space” (Data Hall)
This is the secure room where the servers and equipment actually live—the “crown jewels” of the physical facility.
- What it is: The inner sanctum. Access here is the most restrictive. This often involves “man-traps” (two-door interlock systems) that only allow one person through at a time, biometric scanners (fingerprint, iris, or facial recognition), and constant, high-definition video monitoring.
- Why it matters: Only pre-authorized, verified personnel should ever be in this room. This layer ensures that even if someone gets inside the building, they can’t get near the equipment.
Layer 4: The Rack & Cabinet
We’re now inside the data hall, but the security doesn’t stop. The individual server racks provide the fourth layer.
- What it is: Secure, lockable server cabinets or cages (in co-location facilities).
- Why it matters: This layer prevents tampering or theft by individuals who may be authorized to be in the data hall but not authorized to access your specific hardware. It compartmentalizes security within the room itself.
Layer 5: The Network (The Digital Perimeter)
Layers 1-4 were physical. Now, we move to the logical (digital) security that protects the data in transit.
- What it is: This is your digital “moat.” It includes robust firewalls, Intrusion Detection Systems (IDS), Intrusion Prevention Systems (IPS), and DDoS (Distributed Denial of Service) protection.
- Why it matters: This layer filters all incoming and outgoing traffic. It’s designed to block malicious actors, malware, and viruses before they can ever reach your systems, just as a physical patrol stops an intruder at the fence.
Layer 6: The Host (The Server Itself)
If a threat were to bypass the network, it would next try to attack the server or operating system.
- What it is: Securing the individual machines. This involves OS hardening (disabling unnecessary services), diligent patch management (always being up-to-date), and robust anti-virus/anti-malware software.
- Why it matters: An unpatched server is like an unlocked door. This layer ensures each individual machine is as “locked down” and resilient as possible.
Layer 7: The Data (The Crown Jewels)
This is the final and most crucial layer. If all else fails, how do you protect the data itself?
- What it is: Data encryption. Data should be encrypted “at rest” (when it’s sitting on a hard drive) and “in transit” (when it’s moving over the network). This layer also includes strong user access controls, multi-factor authentication (MFA), and Data Loss Prevention (DLP) policies.
- Why it matters: Even if an intruder physically stole a hard drive (breaching Layers 1-4) and bypassed the network (Layers 5-6), encrypted data would be unreadable and useless to them.
Your Fortress is Only as Strong as Its Weakest Layer
Protecting a data center isn’t about choosing between physical security and cybersecurity. It’s about creating a single, unified strategy where every layer supports the others.
The best data center security practices recognize that a digital firewall (Layer 5) is useless if someone can walk in and steal the server (breaching Layers 1-4). Likewise, the strongest fence in the world (Layer 1) won’t stop a hacker who can exploit an unpatched server (Layer 6).
By implementing a robust 7-layer model, you build a true digital fortress that protects your organization’s most valuable asset from every conceivable angle.