The True Cost of “Checking the Box” on Cybersecurity Compliance
While Cybersecurity Compliance is a regulatory necessity, viewing it as the ultimate objective is a strategic failure. Relegating compliance to a purely administrative function creates a misalignment between perceived safety and actual risk posture. This “compliance-first” mentality fosters a false sense of security, leaving critical vulnerabilities within the defense architecture unaddressed. Furthermore, it results in significant budgetary inefficiency. For the modern CISO, distinguishing between regulatory adherence and genuine security resilience is paramount to avoiding the hidden costs of superficial compliance.
The False Economy of Compliance-Only Spending
The moment an organization focuses solely on meeting the minimum requirements of a framework (like HIPAA, GDPR, or SOC 2) without considering actual threat vectors, the security budget becomes an expense, not an investment.
The Cost of a Breach in a Compliant Environment
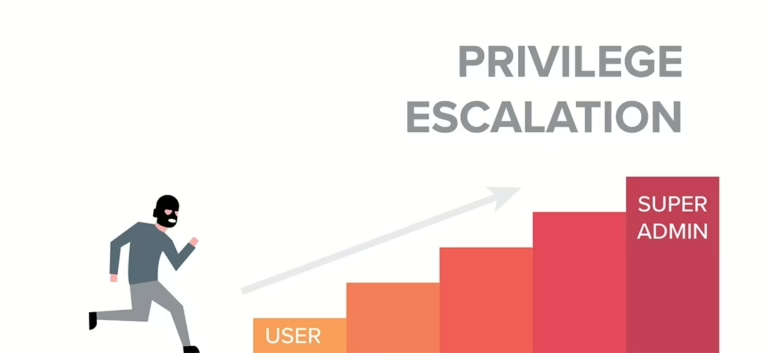
The most devastating cost of checking the box on Cybersecurity Compliance is the resulting breach. Compliance does not prevent sophisticated attacks.
Shifting from Compliance to Risk Management
The strategic CISO uses Cybersecurity Compliance as a floor, not a ceiling. The goal must shift from achieving a compliance checklist to managing true risk exposure.
In conclusion, relying on superficial adherence to Cybersecurity Compliance is a costly gamble. It creates vulnerabilities, wastes capital on ineffective controls, and offers little defense against modern attackers. By making security a strategic driver and viewing compliance as a necessary outcome of effective risk management, organizations can eliminate the hidden costs and achieve true, measurable protection. In the digital-first era, data is often a company’s most valuable asset. But with great value comes great responsibility. For many businesses, terms like “GDPR,” “HIPAA,” or “PCI DSS” sound like a bureaucratic nightmare—a series of complex, expensive hurdles. It’s tempting to view cybersecurity compliance as just another “checkbox” to tick off.
But this perspective is dangerous.
In reality, cybersecurity compliance and regulations are not the goal; they are the baseline. They are the fundamental framework designed to protect your customers, your reputation, and your bottom line from catastrophic failure. Ignoring them, or treating them as a mere suggestion, is a high-stakes gamble you can’t afford to take.
This article explores why compliance is a critical pillar of a modern security strategy, not just a legal burden.
What Is Cybersecurity Compliance? (And What It’s Not)
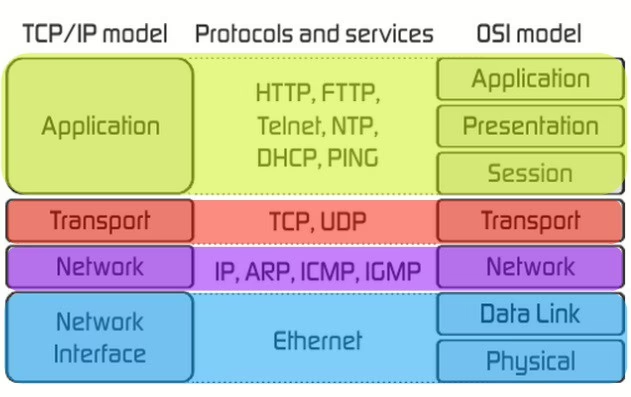
It’s important to understand the difference between two key terms:
You can be “secure” without being “compliant” (though it’s rare). More frighteningly, you can be “compliant” without being truly “secure.” A company can check all the boxes on an audit form but still have a weak security culture.
A strong security posture, however, uses compliance as a roadmap to build a robust, defensible, and trustworthy operation.
Why Compliance Can’t Be Ignored
For businesses wondering why they should invest heavily in compliance, the motivations are crystal clear and stack up quickly.
1. Avoiding Crippling Financial Penalties
Regulators are no longer lenient. The fines for non-compliance are designed to be a deterrent, and they are succeeding.
2. Protecting Your Most Valuable Asset: Trust
A data breach is a public event. When customers trust you with their personal information, a breach feels like a personal betrayal. The cost of a breach isn’t just the fine; it’s the long-term reputational damage and customer churn that follows. Building trust is hard, but destroying it is frighteningly easy.
3. The Shift from “If” to “When”
The modern threat landscape is not a matter of if you will be targeted, but when. Compliance frameworks are built from the collective “lessons learned” of thousands of data breaches. They provide a proven playbook for:
A Quick Guide to the “Alphabet Soup” of Regulations
While the specific rules that apply to you depend on your industry and location, here are the most common frameworks businesses encounter:
5 Practical Steps to Building a Compliant Security Program
Navigating this landscape can feel overwhelming. Here is a practical, step-by-step approach.
Step 1: Discover and Assess
You cannot protect what you do not know. The first step is a thorough risk assessment.
Step 2: Establish Policies and Controls
Develop clear, written security policies. This isn’t just for a binder on a shelf; this is the rulebook for your entire company. This includes access control, password policies, data disposal, and acceptable use.
Step 3: Implement Your Controls
This is where technology and people meet. Implement your firewalls, endpoint detection, and encryption. Crucially, train your people. Your employees are a core part of your defense, and they must be trained to spot phishing attempts and follow security protocols.
Step 4: Monitor, Test, and Audit
Compliance is not a “set it and forget it” project. It is a continuous process.
Step 5: Plan Your Response
Have an Incident Response Plan ready before you need it. Who do you call? How do you communicate with customers? How do you isolate the threat? A calm, prepared response can save your business.
Compliance Is Your Business Shield
Cybersecurity compliance and regulations are not the enemy. They are a strategic framework for managing risk in an increasingly hostile digital world. By embracing compliance, you are not just avoiding fines; you are building a more resilient, efficient, and trustworthy business. You are sending a clear message to your customers, partners, and competitors that you take security seriously.