Essential System Management Policies for Enhanced Security
Introduction to System Management Policies In addition to establishing policies for users, it is crucial to have well-defined policies…
Cyber Security

Introduction to System Management Policies In addition to establishing policies for users, it is crucial to have well-defined policies…
In today’s technology-driven era, the importance of a robust cybersecurity framework for any private or public organization cannot be…
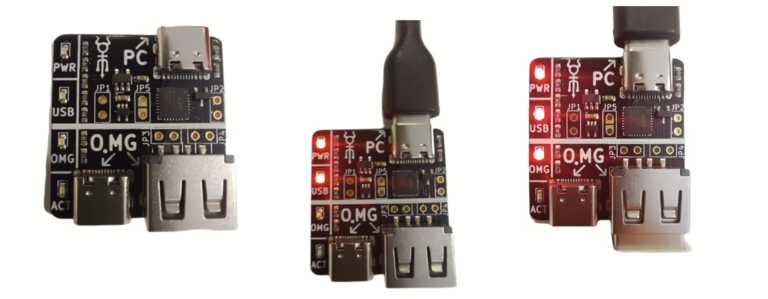
O.MG Cable: A Comprehensive Overview As technology advances, so do the tools and techniques used in cybersecurity, both for…

Unveiling Microsoft Advanced Threat Analytics (ATA) Microsoft Advanced Threat Analytics (ATA) is a powerful tool designed to safeguard organizations…

What is a MAC Address? A MAC address, or Media Access Control address, is a unique identifier assigned to…

What is IP Spoofing? IP spoofing, also known as IP address forgery, is a technique used by hackers to…

Understanding Honeypots in Cybersecurity A honeypot is a unique security mechanism designed to simulate a server or an entire…

As technology advances, accessing and utilizing information has become significantly easier. However, this progress has also benefited cyber attackers,…

Is Windows Defender enough in 2025? We tested the top 12 antivirus suites for malware detection, system impact, and…

In the dynamic cyber landscape of today, effective security requires a comprehensive, multi-layered strategy. Simply relying on a single…
End of content
End of content