Understanding General Data Protection Regulations: A Comprehensive Guide
What is GDPR? The General Data Protection Regulation (GDPR) is a landmark law established by the European Union in…
Cyber Security

What is GDPR? The General Data Protection Regulation (GDPR) is a landmark law established by the European Union in…
Penetration Testing in Embedded Systems: A Critical Cybersecurity Component In today’s digital landscape, penetration testing has become a crucial…

Navigating the Evolving Landscape of Cybersecurity Threats and Trends In the realm of cybersecurity, technological advancements are a double-edged…

Understanding Ethical Hacking Hacking, often translated as computer hacking, refers to gaining unauthorized access to an electronic system. While…
Intrusion Detection Systems (IDS) are security applications designed to detect malicious activities within your network traffic. The primary goal…

Cast your mind back to May of this year: Congress was deeply involved in debates over a massive budget…
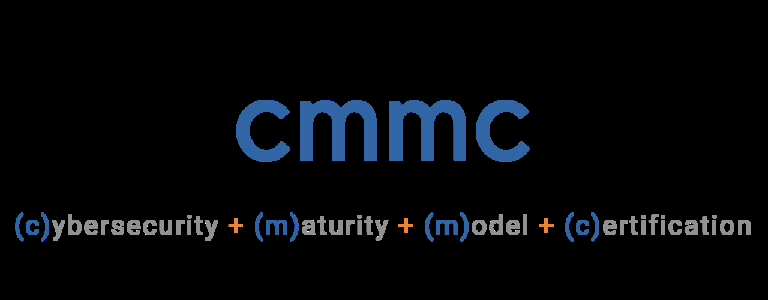
Mastering CMMC: Your Essential Guide to Cybersecurity Maturity Model Certification The Department of Defense (DoD) has introduced the Cybersecurity…
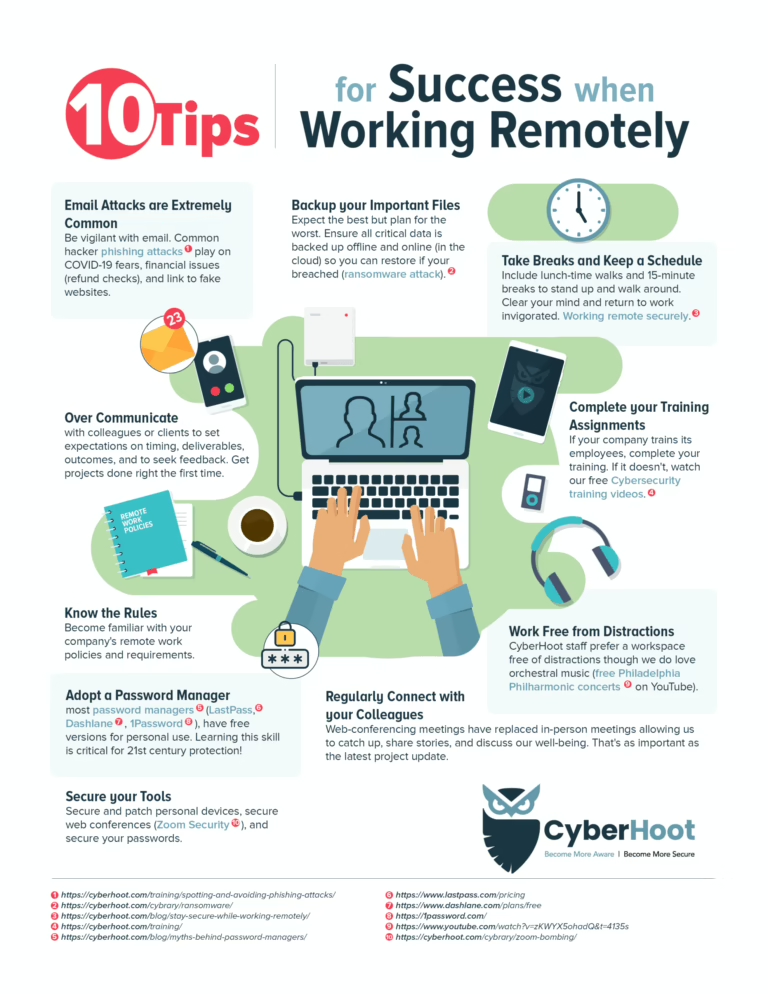
Mastering Remote Work Security: Expert Tips for Business Success The COVID-19 pandemic has dramatically reshaped our work environment, with…

Secure Business Integration – Artificial Intelligence (AI) is entering the business world with the enthusiasm of a new intern,…

Zero Trust RPAM – The global workforce has undergone a seismic shift since the onset of COVID-19. The traditional…
End of content
End of content