Mastering HITECH Act Compliance: Your Ultimate Guide to Healthcare Data Security
The Health Information Technology for Economic and Clinical Health (HITECH) Act, enacted in 2009, is a pivotal piece of…
Cyber Security

The Health Information Technology for Economic and Clinical Health (HITECH) Act, enacted in 2009, is a pivotal piece of…

Understanding Passwords and Their Vital Role Passwords are the cornerstone of cybersecurity, serving as the first line of defense…

Understanding the Internet of Things (IoT) The Internet of Things (IoT) refers to any device or machine capable of…
In the realm of computer science, particularly in cybersecurity and software development, there exist numerous powerful and intriguing techniques….
What is Server Side Request Forgery (SSRF)? Server Side Request Forgery, or SSRF, is a sneaky cyber vulnerability that…

The Evolution of Secure Communication From ancient times to the digital age, the need for secure communication has been…
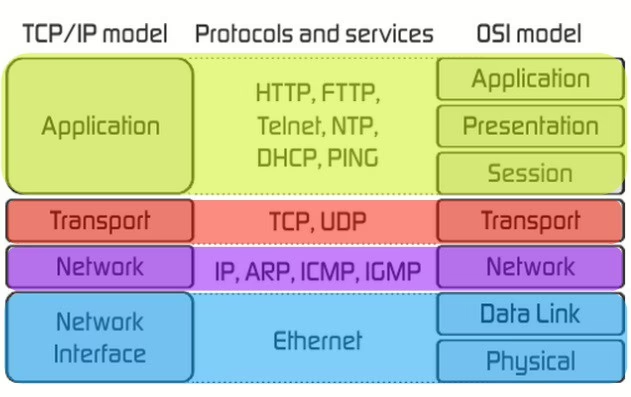
Understanding OSI and TCP/IP Models The OSI model defines how devices communicate over networks. Developed by the International Organization…
Introduction to Nishang Nishang is an exceptional post-exploitation toolkit crafted by Nikhil Mittal. This powerful toolkit comprises a collection…

Introduction to CMMC The Cybersecurity Maturity Model Certification (CMMC) framework is a standard developed by the Department of Defense…

Mastering Europrivacy Hybrid Certification for GDPR Compliance The General Data Protection Regulation (GDPR) has always needed a unified certification…
End of content
End of content