Beware of Fake CAPTCHA Traps: The Hidden Threat to Your Cybersecurity
Unmasking Fake CAPTCHA Traps In the ever-evolving digital landscape, fake CAPTCHA screens have surfaced as a cunning ploy by…
Cyber Security
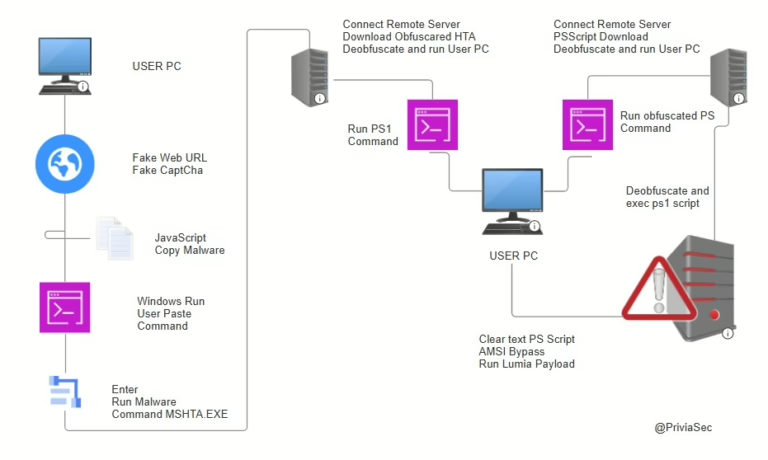
Unmasking Fake CAPTCHA Traps In the ever-evolving digital landscape, fake CAPTCHA screens have surfaced as a cunning ploy by…
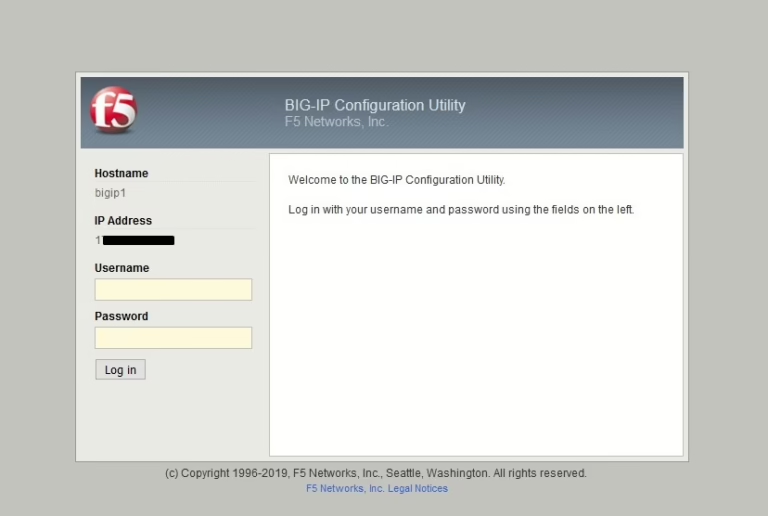
F5 BIG-IP CVE-2021-22986: Unmasking the Latest Security Threat A fresh vulnerability has surfaced following the update for the Unauthenticated…
The Facebook Data Breach: What Went Down? Just last weekend, a hacker forum dropped a bombshell: a colossal data…

Disaster Recovery: Your Business’s Lifeline In the fast-paced world of business, disaster recovery, access rights, and core security principles…

What Are Ransom DDoS Attacks? A Ransom Distributed Denial of Service (DDoS) attack, or RDDOS, is a cyber shakedown….
Unveiling the WHO-Gates Plan: Global Digital ID & AI Surveillance Explained The World Health Organization (WHO), with the backing…

Unmasking Prompt Injection Attacks Prompt injection attacks are a growing concern in the world of artificial intelligence. These sophisticated…

What is Cross-Site Request Forgery (CSRF)? Cross-Site Request Forgery (CSRF) is a sneaky web vulnerability that tricks users into…
Dive into REST API Fuzzing As tech advances, apps are shifting to platform-independent structures. To make this happen, services…

Getting to Grips with Cross-Site Scripting (XSS) Cross-Site Scripting, or XSS for short, is a sneaky security loophole that…
End of content
End of content