Massive Twitter Bitcoin Scam: How Hackers Stole Thousands from High-Profile Accounts
Twitter Bitcoin Scam – Wave of cyber attacks, hackers targeted and compromised the verified Twitter accounts of several prominent figures and companies in a recent . Among the affected were Elon Musk, Jeff Bezos, Bill Gates, and major corporations like Apple, Binance, and Coinbase. The attackers then tweeted from these accounts, promising to double any Bitcoin sent to a specified address. This elaborate scam resulted in the attackers amassing approximately 12.8 Bitcoin.
Twitter’s Response to the Security Breach
Twitter released a statement explaining that the attackers used social engineering tactics to target Twitter employees who had access to internal systems. In an attempt to contain the situation, Twitter temporarily restricted tweeting from verified accounts. However, the attack persisted for several hours. During this time, followers of these high-profile accounts continued to send Bitcoin to the specified address, believing the promises made in the tweets.
Notably, tweets from Elon Musk’s account were repeatedly posted even after deletion, and different Bitcoin addresses were used in direct messages. Twitter announced that it would limit the activities of verified accounts until the issue was fully resolved.
Critical Vulnerability in Windows DNS Server
CheckPoint researchers discovered a critical vulnerability, named ‘SigRed,’ affecting Windows Server operating systems from 2003 to 2019. This vulnerability, with a CVSS score of 10, allows attackers to gain administrative rights over an organization’s entire IT infrastructure.
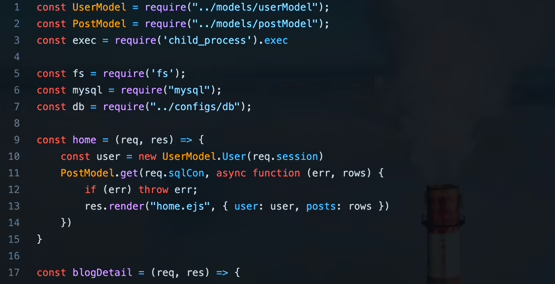
The vulnerability, identified as CVE-2020-1350, arises from the Windows DNS Server service improperly handling incoming requests. An unauthenticated attacker can exploit this by configuring domain NS records to point to a malicious name server and sending malicious DNS queries to the target DNS server, thereby gaining SYSTEM privileges on the target system.
Mitigation and Patches
Microsoft has released security updates to address this vulnerability. Organizations are urged to apply these updates promptly. If updates cannot be applied immediately, the maximum length of DNS messages can be set to ‘0xFF00’ using the following commands:
reg add "HKEY_LOCAL_MACHINESYSTEMCurrentControlSetServicesDNSParameters" /v "TcpReceivePacketSize" /t REG_DWORD /d 0xFF00 /f net stop DNS & net start DNS
Critical RECON Vulnerability in SAP Servers
A critical vulnerability, known as RECON (CVE-2020-6287), has been identified in SAP NetWeaver application servers. This vulnerability, with a CVSS score of 10, affects the LM Configuration Wizard component and allows attackers to gain high-privilege access to SAP NetWeaver application servers without authentication.
Exploiting this vulnerability can enable attackers to alter financial records, access personal information of employees and customers, corrupt system data, delete log records, and interfere with critical business transactions. The affected component is used in various SAP applications, impacting over 40,000 SAP customers.
Affected Versions and Mitigation
The RECON vulnerability is present by default in SAP NetWeaver Application Server versions from 7.3 to 7.5. Organizations using SAP applications are advised to apply the latest patches to mitigate this vulnerability. Additionally, conducting security scans and analyzing high-privilege user activities are recommended.
Adobe Releases Patches for Critical Vulnerabilities
Adobe has released software updates to address 13 new vulnerabilities across five widely used applications. Four of these vulnerabilities are rated as critical. The affected products include:
The Adobe Creative Cloud Desktop Application version 5.1 and earlier has a critical vulnerability (CVE-2020-9682) leading to arbitrary file system write and three important privilege escalation vulnerabilities. Adobe Media Encoder version 14.2 and earlier has two remote code execution vulnerabilities (CVE-2020-9650 and CVE-2020-9646) affecting both Windows and macOS users. Adobe Genuine Service version 6.6 and earlier has three important privilege escalation vulnerabilities affecting Windows and macOS. Adobe Download Manager version 2.0.0.518 has a vulnerability (CVE-2020-9688) that could allow remote code execution.
Adobe recommends users update to the latest versions of these products to protect against these vulnerabilities.